DSA assumes a prime  of typically 2048 bits 7, a prime
of typically 2048 bits 7, a prime  of 256 bits dividing
of 256 bits dividing  , an element
, an element  of order
of order  in the integers modulo
in the integers modulo  , a secret signing key
, a secret signing key  and a public verification key
and a public verification key  . The signature on a message
. The signature on a message  ,
,  , is
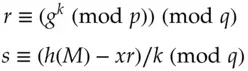
, is  where
where
The hash function used by default is SHA256 8.
DSA is the classic example of a randomised digital signature scheme without message recovery. The most commonly-used version nowadays is ECDSA, a variant based on elliptic curves, which we'll discuss now – this is for example the standard for cryptocurrency and increasingly also for certificates in bank smartcards.
5.7.3 Elliptic curve cryptography
Discrete logarithms and their analogues exist in many other mathematical structures. Elliptic curve cryptography uses discrete logarithms on an elliptic curve – a curve given by an equation like 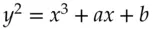 . These curves have the property that you can define an addition operation on them and the resulting Mordell group can be used for cryptography. The algebra gets a bit complex and this book isn't the place to set it out 9. However, elliptic curve cryptosystems are interesting for at least two reasons.
. These curves have the property that you can define an addition operation on them and the resulting Mordell group can be used for cryptography. The algebra gets a bit complex and this book isn't the place to set it out 9. However, elliptic curve cryptosystems are interesting for at least two reasons.
First is performance; they give versions of the familiar primitives such as Diffie-Hellmann key exchange and the Digital Signature Algorithm that use less computation, and also have shorter variables; both are welcome in constrained environments. Elliptic curve cryptography is used in applications from the latest versions of EMV payment cards to Bitcoin.
Second, some elliptic curves have a bilinear pairing which Dan Boneh and Matt Franklin used to construct cryptosystems where your public key is your name [287]. Recall that in RSA and Diffie-Hellmann, the user chose his private key and then computed a corresponding public key. In a so-called identity-based cryptosystem , you choose your identity then go to a central authority that issues you with a private key corresponding to that identity. There is a global public key, with which anyone can encrypt a message to your identity; you can decrypt this using your private key. Earlier, Adi Shamir had discovered identity-based signature schemes that allow you to sign messages using a private key so that anyone can verify the signature against your name [1707]. In both cases, your private key is computed by the central authority using a system-wide private key known only to itself. Identity-based primitives have been used in a few specialist systems: in Zcash for the payment privacy mechanisms, and in a UK government key-management protocol called Mikey-Sakke. Computing people's private keys from their email addresses or other identifiers may seem a neat hack, but it can be expensive when government departments are reorganised or renamed [116]. Most organisations and applications use ordinary public-key systems with certification of public keys, which I'll discuss next.
5.7.4 Certification authorities
Now that we can do public-key encryption and digital signature, we need some mechanism to bind users to keys. The approach proposed by Diffie and Hellman when they invented digital signatures was to have a directory of the public keys of a system's authorised users, like a phone book. A more common solution, due to Loren Kohnfelder, is for a certification authority (CA) to sign the users’ public encryption keys or their signature verification keys giving certificates that contain a user's name, one or more of their public keys, and attributes such as authorisations. The CA might be run by the local system administrator; but it is most commonly a third party service such as Verisign whose business is to sign public keys after doing some due diligence about whether they are controlled by the principals named in them.
A certificate might be described symbolically as
(5.1) 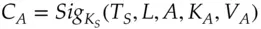
where  is the certificate's starting date and time,
is the certificate's starting date and time,  is the length of time for which it is valid, A is the user's name,
is the length of time for which it is valid, A is the user's name,  is her public encryption key, and
is her public encryption key, and  is her public signature verification key. In this way, only the administrator's public signature verification key needs to be communicated to all principals in a trustworthy manner.
is her public signature verification key. In this way, only the administrator's public signature verification key needs to be communicated to all principals in a trustworthy manner.
Certification is hard, for a whole lot of reasons. Naming is hard, for starters; we discuss this in Chapter 7on Distributed Systems. But often names aren't really what the protocol has to establish, as in the real world it's often about authorisation rather than authentication. Government systems are often about establishing not just a user's name or role but their security clearance level. In banking systems, it's about your balance, your available credit and your authority to spend it. In commercial systems, it's often about linking remote users to role-based access control. In user-facing systems, there is a tendency to dump on the customer as many of the compliance costs as possible [524]. There are many other things that can go wrong with certification at the level of systems engineering. At the level of politics, there are hundreds of certification authorities in a typical browser, they are all more or less equally trusted, and many nation states can coerce at least one of them 10. The revocation of bad certificates is usually flaky, if it works at all. There will be much more on these topics later. With these warnings, it's time to look at the most commonly used public key protocol, TLS.
Читать дальше

 of typically 2048 bits 7, a prime
of typically 2048 bits 7, a prime  of 256 bits dividing
of 256 bits dividing  , an element
, an element  of order
of order  in the integers modulo
in the integers modulo  , a secret signing key
, a secret signing key  and a public verification key
and a public verification key  . The signature on a message
. The signature on a message  ,
,  , is
, is  where
where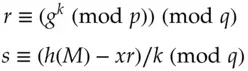
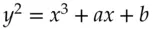 . These curves have the property that you can define an addition operation on them and the resulting Mordell group can be used for cryptography. The algebra gets a bit complex and this book isn't the place to set it out 9. However, elliptic curve cryptosystems are interesting for at least two reasons.
. These curves have the property that you can define an addition operation on them and the resulting Mordell group can be used for cryptography. The algebra gets a bit complex and this book isn't the place to set it out 9. However, elliptic curve cryptosystems are interesting for at least two reasons.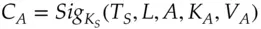
 is the certificate's starting date and time,
is the certificate's starting date and time,  is the length of time for which it is valid, A is the user's name,
is the length of time for which it is valid, A is the user's name,  is her public encryption key, and
is her public encryption key, and  is her public signature verification key. In this way, only the administrator's public signature verification key needs to be communicated to all principals in a trustworthy manner.
is her public signature verification key. In this way, only the administrator's public signature verification key needs to be communicated to all principals in a trustworthy manner.









