Ross Anderson - Security Engineering
Здесь есть возможность читать онлайн «Ross Anderson - Security Engineering» — ознакомительный отрывок электронной книги совершенно бесплатно, а после прочтения отрывка купить полную версию. В некоторых случаях можно слушать аудио, скачать через торрент в формате fb2 и присутствует краткое содержание. Жанр: unrecognised, на английском языке. Описание произведения, (предисловие) а так же отзывы посетителей доступны на портале библиотеки ЛибКат.
- Название:Security Engineering
- Автор:
- Жанр:
- Год:неизвестен
- ISBN:нет данных
- Рейтинг книги:3 / 5. Голосов: 1
-
Избранное:Добавить в избранное
- Отзывы:
-
Ваша оценка:
Security Engineering: краткое содержание, описание и аннотация
Предлагаем к чтению аннотацию, описание, краткое содержание или предисловие (зависит от того, что написал сам автор книги «Security Engineering»). Если вы не нашли необходимую информацию о книге — напишите в комментариях, мы постараемся отыскать её.
secure? Understand how to engineer dependable systems with this newly updated classic
In
Cambridge University professor Ross Anderson updates his classic textbook and teaches readers how to design, implement, and test systems to withstand both error and attack.
This book became a best-seller in 2001 and helped establish the discipline of security engineering. By the second edition in 2008, underground dark markets had let the bad guys specialize and scale up; attacks were increasingly on users rather than on technology. The book repeated its success by showing how security engineers can focus on usability.
Now the third edition brings it up to date for 2020. As people now go online from phones more than laptops, most servers are in the cloud, online advertising drives the Internet and social networks have taken over much human interaction, many patterns of crime and abuse are the same, but the methods have evolved. Ross Anderson explores what security engineering means in 2020, including:
How the basic elements of cryptography, protocols, and access control translate to the new world of phones, cloud services, social media and the Internet of Things Who the attackers are – from nation states and business competitors through criminal gangs to stalkers and playground bullies What they do – from phishing and carding through SIM swapping and software exploits to DDoS and fake news Security psychology, from privacy through ease-of-use to deception The economics of security and dependability – why companies build vulnerable systems and governments look the other way How dozens of industries went online – well or badly <l

 which he shares with Alice, and another key
which he shares with Alice, and another key  which he shares with Bob. So long as he continues to sit in the middle of the network and translate the messages between them, they may have a hard time detecting that their communications are compromised. The usual solution is to authenticate transient keys, and there are various possibilities.
which he shares with Bob. So long as he continues to sit in the middle of the network and translate the messages between them, they may have a hard time detecting that their communications are compromised. The usual solution is to authenticate transient keys, and there are various possibilities. and the generator
and the generator  are public values chosen in some suitable way, and that each user who wishes to sign messages has a private signing key
are public values chosen in some suitable way, and that each user who wishes to sign messages has a private signing key  with a public signature verification key
with a public signature verification key  . An ElGamal signature scheme works as follows. Choose a message key
. An ElGamal signature scheme works as follows. Choose a message key  at random, and form
at random, and form  (mod
(mod  ). Now form the signature
). Now form the signature  using a linear equation in
using a linear equation in  ,
,  , the message
, the message  and the private key
and the private key  . There are a number of equations that will do; the one that happens to be used in ElGamal signatures is
. There are a number of equations that will do; the one that happens to be used in ElGamal signatures is
 is computed as
is computed as  ; this is done modulo
; this is done modulo  . When both sides are passed through our one-way homomorphism
. When both sides are passed through our one-way homomorphism  mod
mod  we get:
we get: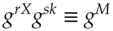

 consists of the values
consists of the values  and
and  , and the recipient can verify it using the above equation.
, and the recipient can verify it using the above equation. and
and  can weaken the algorithm. We will also want to hash the message
can weaken the algorithm. We will also want to hash the message  using a hash function so that we can sign messages of arbitrary length, and so that an opponent can't use the algorithm's algebraic structure to forge signatures on messages that were never signed. Having attended to these details and applied one or two optimisations, we get the Digital Signature Algorithm (DSA) which is a US standard and widely used in government applications.
using a hash function so that we can sign messages of arbitrary length, and so that an opponent can't use the algorithm's algebraic structure to forge signatures on messages that were never signed. Having attended to these details and applied one or two optimisations, we get the Digital Signature Algorithm (DSA) which is a US standard and widely used in government applications.









