1 ...7 8 9 11 12 13 ...22 But when multiple nodes can share a medium, as they did with early Ethernet, things get tricky. At this point you're rightly thinking that with the exception of wireless, nobody connects nodes to a shared medium anymore. Hubs went out of fashion long ago. Now we connect devices to switches (the marketing term for bridges). However, switches actually simulate the behavior of a shared medium. Time for a quick history lesson.
A Brief History of Ethernet
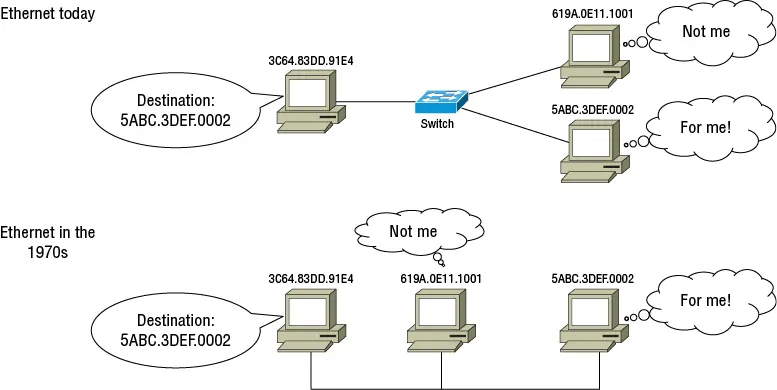
The original Ethernet standards from the 1970s were designed for nodes all connected to a shared electrical bus that often took the form of a thick yellow cable (you may have heard the term Thicknet). Whenever one node would transmit a signal, all other nodes connected to the cable would receive it. Communication was half-duplex, and all nodes were in the same collision domain. As a way of detecting errors introduced by collisions, the original Ethernet II (DIX) specification got a frame check sequence (FCS, sometimes called a cyclic redundancy check, or CRC) to detect errors. Even today as back then, nodes discard frames that fail the FCS check.
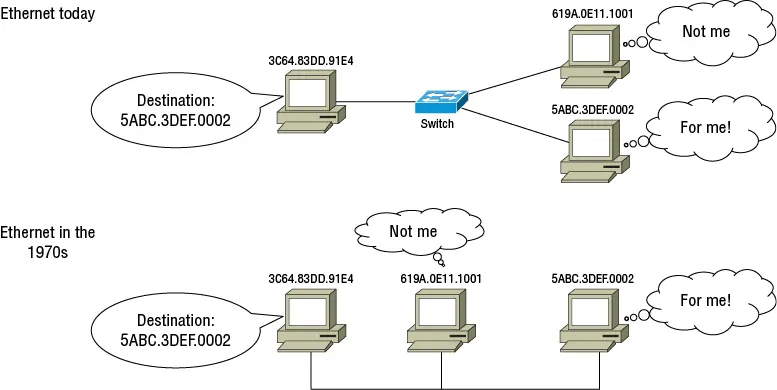
The multi-access nature of Ethernet made it necessary to assign each node's network interface a unique, 48-bit Media Access Control (MAC) address. The sending node would construct a frame that included the destination node's MAC address and the data to send. All nodes would receive the frame, but only the destination node would process it.
Now let's fast-forward to today. We still use MAC addresses, even though the original rationale for using them is long gone. To maintain backward compatibility over the years, we never got rid of them. Figure 1.3shows the original DIX frame format that we still use today. We're still using a technology designed specifically for devices that were all sharing a thick yellow cable. Today, however, instead of nodes sharing this thick yellow cable, they're connected to a switch.
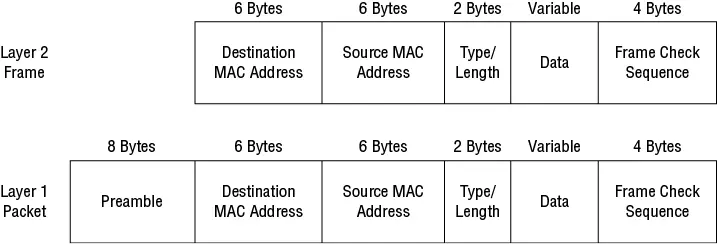
Figure 1.3 Layer 2 frame and layer 1 packet, structurally identical to the revised (1997) IEEE 802.3 format that we use today
 You may have seen diagrams that show the Ethernet frame with an 8-byte preamble at the beginning. The preamble is not actually part of the frame but is a series of bits that provide clock synchronization for the Physical layer and signal the start of the frame. The entire collection of bits—including the preamble and frame—compose a layer 1 Ethernet packet. Although most of the time when you hear “packet” it refers to an IP packet (layer 3), “packet” is a generic term for any PDU. To avoid confusion, you can think of the raw bits as a layer 1 Ethernet PDU.
You may have seen diagrams that show the Ethernet frame with an 8-byte preamble at the beginning. The preamble is not actually part of the frame but is a series of bits that provide clock synchronization for the Physical layer and signal the start of the frame. The entire collection of bits—including the preamble and frame—compose a layer 1 Ethernet packet. Although most of the time when you hear “packet” it refers to an IP packet (layer 3), “packet” is a generic term for any PDU. To avoid confusion, you can think of the raw bits as a layer 1 Ethernet PDU.
Switches replace the shared cable of the early Ethernet with multiple cables, breaking the inherent broadcast nature of the thick yellow cable. Switches thus have to perform some interesting hackery to maintain backward compatibility with the early Ethernet standards. When a switch receives an Ethernet frame, by default it forwards that frame to all other devices connected to the switch—a process called flooding or broadcasting. This creates the illusion that all nodes are connected to the same thick yellow cable. (In networking parlance, they're all in the same broadcast domain or segment.) This illusion is called transparent bridging (aka switching) because to the nodes, the switch is invisible. Incidentally, you'll recognize this simulated yellow cable by its common name: a local area network (LAN).
Although switches eliminate collision domains by offering full-duplex communication, they still waste bandwidth by flooding traffic to nodes that don't need it. To mitigate flooding, switches implement a form of routing. When a switch receives a frame on an interface, it records the ingress interface and source MAC address in its MAC address table. Subsequently, when a switch receives a frame destined for that same MAC address, it queries the MAC address table, which returns the interface number. The switch then forwards the frame only out of that interface, rather than flooding it.
The MAC address table is stored in a type of memory called content-addressable memory (CAM). CAM is often used as a synonym for the MAC address table. The CAM takes a MAC address and VLAN as input and returns an interface name and number as the output. CAM provides faster read times than RAM.
SW3#show mac address-table dynamic Mac Address Table ------------------------------------------- Vlan Mac Address Type Ports ---- ----------- -------- ----- 1 0c3c.8a00.5e02 DYNAMIC Gi0/2 1 0c3c.8ad7.9101 DYNAMIC Gi0/2 1 0c3c.8afd.c101 DYNAMIC Gi0/1 1 0c3c.8afd.c102 DYNAMIC Gi0/2 10 0c3c.8ad7.800a DYNAMIC Gi0/0 20 0c3c.8ad7.8014 DYNAMIC Gi0/0 Total Mac Addresses for this criterion: 6
 The use of the MAC address table changes the fundamental nature of MAC addresses. They no longer function as just names for identification, but also as addresses for location.
The use of the MAC address table changes the fundamental nature of MAC addresses. They no longer function as just names for identification, but also as addresses for location.
On the other hand, if a switch receives a frame for a MAC address that doesn't have a mapping in the MAC address table—called an unknown unicast—it reverts to its default behavior and floods the frame out of all other interfaces.
Unknown unicasts are more common than you might think. Entries in the MAC address table don't last forever. By default, a MAC address entry is deleted or ages out 300 seconds (5 minutes) after the switch last sees the traffic from the MAC address. Note that aging time is not based on when the entry was created.
SW3#show mac address-table aging-time vlan 1 Global Aging Time: 300 Vlan Aging Time ---- ---------- 1 300
You can adjust the global aging time to between 10 and 1,000,000 seconds or disable aging by setting the aging time to 0.
SW3(config)#mac address-table aging-time ? <0-0> Enter 0 to disable aging <10-1000000> Aging time in seconds
You can also adjust the aging time on a per-VLAN basis.
SW3(config)#mac address-table aging-time 300 vlan ? <1-4094> VLAN id
Disabling aging might sound like a good idea, as it would prevent flooding, right? Not necessarily. The CAM has a finite amount of space, and once the MAC address table is full, the switch will flood traffic to every destination MAC not in the table.
The MAC address table mitigates flooding but doesn't eliminate it. The fundamental flooding behavior of Ethernet remains. To make matters worse, Ethernet implements a special MAC address called a broadcast address (FFFF.FFFF.FFFF). Frames sent to this address are flooded out of all ports. You can imagine the number of major outages that arose from this unwise decision!
The end result is that any node in a broadcast domain can send a frame to another node and the destination node will receive it. We may have added more cables and more devices, but the fundamental behavior of Ethernet hasn't changed in 50 years, as shown in Figure 1.4. When it comes to networking, history has a way of repeating itself.
Читать дальше
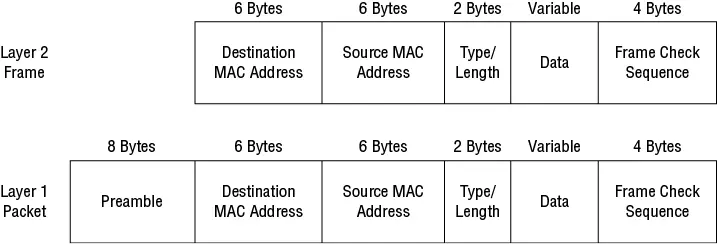
 You may have seen diagrams that show the Ethernet frame with an 8-byte preamble at the beginning. The preamble is not actually part of the frame but is a series of bits that provide clock synchronization for the Physical layer and signal the start of the frame. The entire collection of bits—including the preamble and frame—compose a layer 1 Ethernet packet. Although most of the time when you hear “packet” it refers to an IP packet (layer 3), “packet” is a generic term for any PDU. To avoid confusion, you can think of the raw bits as a layer 1 Ethernet PDU.
You may have seen diagrams that show the Ethernet frame with an 8-byte preamble at the beginning. The preamble is not actually part of the frame but is a series of bits that provide clock synchronization for the Physical layer and signal the start of the frame. The entire collection of bits—including the preamble and frame—compose a layer 1 Ethernet packet. Although most of the time when you hear “packet” it refers to an IP packet (layer 3), “packet” is a generic term for any PDU. To avoid confusion, you can think of the raw bits as a layer 1 Ethernet PDU.