In risk analysis, it is important to identify all the relevant hazardous events. The hazardous events may be (i) random, such as technical failures and natural events (e.g. lightning, flooding), (ii) systematic , such as software bugs or erroneous installation, or (iii) due to deliberate actions, such as computer hacking and arson. The term safety is often used when we talk about random events, whereas security is used in relation to deliberate actions. The term total safety is sometimes used to cover both safety and security. Security assessment is discussed in Chapter 17.
Definition 2.33(Security)
Freedom from, or resilience against, harm committed by hostile threat actors.
Security is, as safety, a relative concept that is closely related to risk acceptability. The principal difference between safety and security is intentionality ; security is characterized by adversary intent to do harm. Assessing security risk therefore changes the first question of Kaplan and Garrick (1981) into how someone can make something happen. This complicates risk assessment, as the range of possible events is restricted only by the assessor's imagination and ability to put herself in the situation of a potential enemy or criminal.
Central to an understanding of the concept of security are the terms threat , threat actor , and vulnerability :
A generic category of an action or event that has the potential to cause damage to an asset.
The deliberate hostile action can be a physical attack, such as arson, sabotage, and theft, or a cyberattack. The generic categories of attacks are called threats, and the entity using a threat is called a threat actor or a threat agent. Arson is therefore a threat, and an arsonist is a threat actor. The threat actor may be a disgruntled employee, a single criminal, a competitor, a group, or even a country. When a threat actor attacks, she seeks to exploit some weaknesses of the item. Such a weakness is called a vulnerability of the item. Weak passwords and heaps of combustible materials close to the item are examples of vulnerabilities.
There are two categories of threats, (i) physical threats and (ii) cyber threats. Cyber threats include hacking, worms, viruses, malware, trojan horses, password cracking, and many more. With our increasing dependency of computers and communication networks, our fear of cyber threats is steadily increasing.
Remark 2.8 (Natural threat)
The word “threat” is also used for potential natural events, such as avalanche, earthquake, flooding, hurricane, landslide, lightning, pandemic, tsunami, and wildfire, to name a few. We may, for example, say that earthquake is a threat to our system. No threat actor is involved for this type of threats.
The term threat actor is used to indicate an individual or a group that can manifest a threat. When analyzing security risk, it is fundamental to identify who could want to exploit the vulnerabilities of a system, and how they might use them against the system.
Definition 2.35 (Threat actor)
An individual, a group or a thing that acts, or has the power to act, to cause, carry, transmit, or support a threat.
A threat actor is sometimes called a threat agent . An example of a threat agent is a hacker who breaks into computers, usually by gaining access to administrative controls.
To cause harm, a threat agent must have the intention , capacity , and opportunity to cause harm. Intention means the determination or desire to achieve an objective. Capacity refers to the ability to accomplish the objective, including the availability of tools and techniques as well as the ability to use these correctly. Opportunity to cause harm implies that the asset must be vulnerable to attack.
Vulnerability may be defined as follows:
Definition 2.36 (Vulnerability)
A weakness of an asset or control that can be exploited by one or more threat actors.
A vulnerability is a characteristic or state of the asset that allows a threat actor to carry out a successful attack. The weakness may have been introduced during design, installation, operation, or maintenance.
Vulnerability refers to the security flaws in a system that allow an attack to be successful. These weaknesses may be categorized as physical, technical, operational, and organizational. A vulnerability in security terms can be, for example, an unlocked door, allowing unauthorized people to access a computer that is not protected by a password. We can see that a vulnerability in many respects can be compared to what we would call “lack of” or “weak” barriers when we are talking about risk.
Vulnerability is also used in relation to safety, but then more as an opposite to resilience (see next section). Security and security assessment are discussed in more detail in Chapter 17.
Figure 2.7shows that a threat agent may use a threat to launch an attack intended to exploit a vulnerability in the system. If the vulnerability is “penetrated” a hazardous event will occur. The threat actor may in some cases get information about vulnerabilities in the system and choose the type of threat that most likely will make the attack successful (from her point of view).
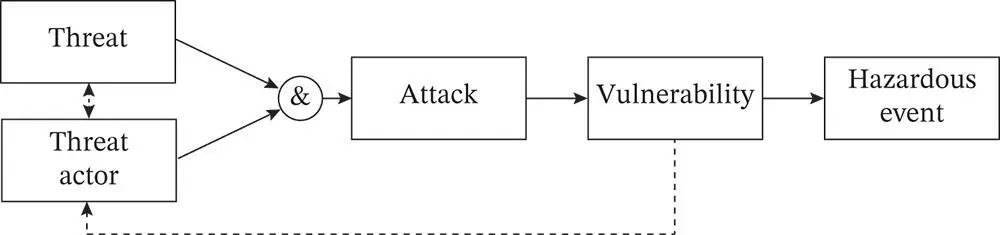 Figure 2.7The concepts of threat, threat actor, and vulnerability.
Figure 2.7The concepts of threat, threat actor, and vulnerability.
Resilience is in many respects the opposite of vulnerability. Foster (1993) defines resilience as:
Definition 2.37 (Resilience)
The ability to accommodate change without catastrophic failure, or the capacity to absorb shocks gracefully.
The word resilience conveys the ability to recover and to be brought back into shape or position after being stressed. Resilience is a broader term than robustness , which is a static concept that is basically synonymous with damage tolerance. In addition to the ability to withstand damage, resilience also has a dynamic component, that is, adaptation to a new situation. Resilience is therefore a pervasive property that influences a system's response to a wide range of stressors and threats (e.g. see Rosness et al. 2004 ; Hollnagel et al. 2006).
1 2.1 Describe the main difference between the concepts of hazard and threat.
2 2.2 What is the difference between a probability and a frequency?
3 2.3 In Table 2.1, various uses of the word “risk” from media are shown. Look at the statements and see if risk should be replaced with another term if we were to apply the definitions used in this book.
4 2.4 Search for the term “hazard” on the Internet and see if it is used in accordance with our definition.
5 2.5 List the possible failure modes of the driver's door on a modern car.
6 2.6 Start with the following situation: You are cycling down a steep road at high speed and approach a major crossing road. Describe a few possible accident scenarios that can develop from this situation. What are the hazards, initiating events and enabling events and conditions in the scenarios that you have described?
7 2.7 Consider the following events related to a ship:The ship hits an obstruction.The crew abandons ship.The captain of a ship is planning a voyage and fails to identify an obstruction in the planning process.The ship sets sail from port.The ship starts sinking.All crew drowns.During the voyage, the person on the bridge of the ship falls asleep.(a) Order these events into a logical accident scenario.(b) Use the definitions of hazardous event and initiating event and identify the steps in the sequence that could be classified as hazardous events and initiating events. Different answers may be relevant, but provide arguments for why you choose as you do.
Читать дальше
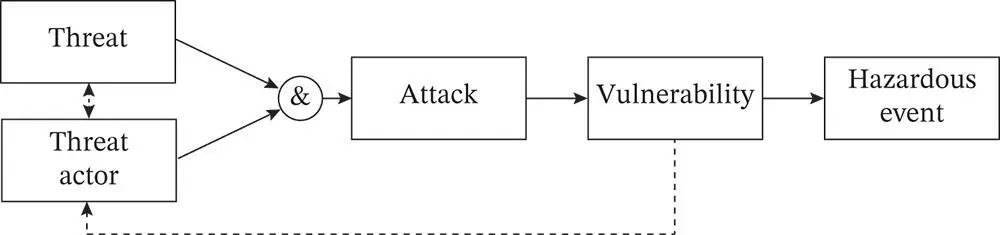 Figure 2.7The concepts of threat, threat actor, and vulnerability.
Figure 2.7The concepts of threat, threat actor, and vulnerability.