Effective security requires a multipronged approach, and Fedora provides effective tools to secure your system in several different ways:
Filtering of network traffic
System activity logging and automatic monitoring tools
Discretionary access controls such as permissions and access control lists
Mandatory access controls through SELinux
Intrusion-detection tools and immutable file attributes to detect and prevent file alteration
Tools to delegate specific system administration privileges to different users
Together with automated software updates, these tools enable you to efficiently maintain your system security.
8.1. Prevent Unwanted Connections
Most Fedora systems are connected to a TCP/IP network. You can guard against unwanted inbound connections to your system by using the built-in firewall.
To adjust the Fedora firewall graphically, select the menu option System→Administration→"Security Level and Firewall." After you enter the root password, the window shown in Figure 8-1 will appear.
Figure 8-1. Firewall configuration tool

The control at the top of this window enables and disables the firewall. When the firewall is enabled, the lower portion of this window can be used to permit connections to your system for selected services; simply select the checkboxes for the desired services. SSH should remain selected to permit secure remote administration.
To permit connections to services that are not listed, click on the triangle for "Other ports." The display will change to reveal an additional section, as shown in Figure 8-2 .
Figure 8-2. Configuring other ports

To add additional ports, click the Add button, and the window shown on the right side of Figure 8-2 will pop up. Enter the port number or the service name, select TCP or UDP for the protocol, and click OK.
A list of most of the common services and their corresponding port numbers can be found in the file /etc/services .
When the firewall is configured to your liking, click OK.
8.1.1.1. Configuring the firewall in text mode
Enter this command:
# lokkit
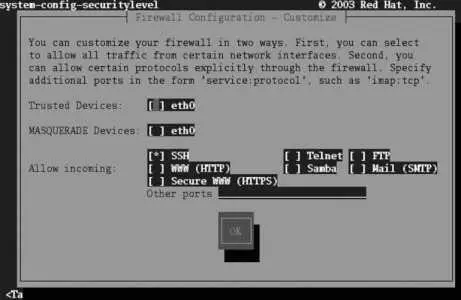
The screen displayed in Figure 8-3 will appear. Use the Tab key to navigate among fields, the spacebar to select and deselect checkboxes, and Enter or the spacebar to activate buttons.
Figure 8-3. Lokkit firewall configuration screen

Enable or disable the firewall using the checkboxes. To customize the types of connections that are permitted through the firewall, tab to the Customize button and press Enter. The customization screen shown in Figure 8-4 will appear.
Figure 8-4. Lokkit firewall customization screen
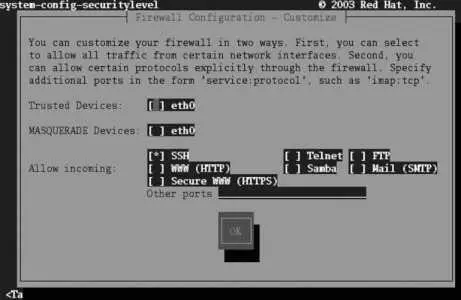
The Trusted Devices and MASQUERADE Devices checkboxes are applicable only to systems with multiple network connections. Do not select either of those options on a system with a single network interface.
The Trusted Devices checkbox will disable firewall protection for the selected interface!
Use the Allow Incoming checkboxes to select the services that will be permitted to connect to your system through the firewall. In almost all cases, SSH should be selected to permit secure remote connections for system administration.
To allow incoming connections to services that are not listed, enter the port number or service, followed by a colon (:), and the protocol (TCP or UDP) into the "Other ports" field at the bottom of the screen. You will need to separate multiple entries with a space or comma. For example, to permit incoming connections to the VNC service as well as to a custom UDP service running on port 64447, use:
vnc:tcp 64447:udp
Select OK to return to the main screen ( Figure 8-3 ); select OK on that screen to save your settings and exit.
8.1.1.2. Temporarily disabling the firewall from the command line
To disable the firewall until the next reboot, stop the iptables service:
# service iptables stop
To reset your firewall to the configured settings, restart the iptables service:
# service iptables restart
The Fedora firewall uses the kernel's iptables capability, which can filter packets based on their source, destination, port, protocol, contents, and current connection state.
To view the current iptables configuration, use the -L option:
# iptables -L
Chain INPUT (policy ACCEPT)
target prot opt source destination
RH-Firewall-1-INPUT all -- anywhere anywhere
Chain FORWARD (policy ACCEPT)
target prot opt source destination
RH-Firewall-1-INPUT all -- anywhere anywhere
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
Chain RH-Firewall-1-INPUT (2 references)
target prot opt source destination
ACCEPT all -- anywhere anywhere
ACCEPT icmp -- anywhere anywhere icmp any
ACCEPT ipv6-crypt-- anywhere anywhere
ACCEPT ipv6-auth-- anywhere anywhere
ACCEPT udp -- anywhere 224.0.0.251 udp dpt:mdns
ACCEPT udp -- anywhere anywhere udp dpt:ipp
ACCEPT tcp -- anywhere anywhere tcp dpt:ipp
ACCEPT all -- anywhere anywhere state RELATED,ESTABLISHED
ACCEPT tcp -- anywhere anywhere state NEW tcp dpt:ssh
REJECT all -- anywhere anywhere reject-with icmp-host-prohibited
There are four chains of rules defined here:
INPUT
Filters packets that are inbound to this system.
FORWARD
Filters packets that are passing through the system. This applies only if there is more than one network interface and IP forwarding is turned on to pass packets between the interfaces (for example, in a system serving as a router).
OUTPUT
Filters packets that are outbound from this system.
RH-Firewall-1-INPUT
This is the chain of rules configured by the firewall system. Notice that this chain is included into the chains for INPUT and FORWARD.
In this example, IPP (Internet Print Protocol, used by CUPS), MDNS (multicast DNS, used by Avahi), and SSH connections are all permitted; only SSH was configured for the firewall, demonstrating that not all services are configured through the firewall configuration tools.
Since the policy for each chain is ACCEPT, flushing (clearing) the rules will result in all packets being accepted. This is exactly what the iptables -F command does, which is executed when the iptables service is stopped.
The graphical firewall configuration tool is system-config-securitylevel (which, in recent versions, also handles SELinux configuration). The character-based version is system-config-securitylevel-tui , which is also known as lokkit . Both of these tools save the firewall configuration in /etc/sysconfig/system-config-securitylevel and, from that configuration, derive a set of iptables rules that are saved in /etc/sysconfig/iptables . That file, in turn, is used by the iptables service ( /etc/init.d/iptables ) to configure the firewall; options that control the operation of the iptables service are stored in /etc/sysconfig/iptables-config .
Читать дальше