Suddenly, the Cubans broke through the South African air defenses and carried out a bombing raid on a South African camp in northern Namibia, killing a number of white conscripts. This proof that their air supremacy had been lost helped the Pretoria government decide to hand over Namibia to the insurgents –itself a huge step on the road to majority rule in South Africa several years later. The raid may also have been the last successful military operation ever carried out by Soviet bloc forces.
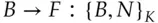
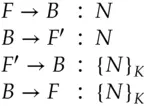
Some years afterwards, a SAAF officer told me how the Cubans had pulled it off. Several MIGs had loitered in southern Angola, just north of the South African air defense belt, until a flight of SAAF Impala bombers raided a target in Angola. Then the MIGs turned sharply and flew openly through the SAAF's air defenses, which sent IFF challenges. The MIGs relayed them to the Angolan air defense batteries, which transmitted them at a SAAF bomber; the responses were relayed back to the MIGs, who retransmitted them and were allowed through – as in Figure 4.2. According to my informant, this shocked the general staff in Pretoria. Being not only outfought by black opponents, but actually outsmarted, was not consistent with the world view they had held up till then.
After this tale was published in the first edition of my book, I was contacted by a former officer in SA Communications Security Agency who disputed the story's details. He said that their IFF equipment did not use cryptography yet at the time of the Angolan war, and was always switched off over enemy territory. Thus, he said, any electronic trickery must have been of a more primitive kind. However, others tell me that ‘Mig-in-the-middle’ tricks were significant in Korea, Vietnam and various Middle Eastern conflicts.
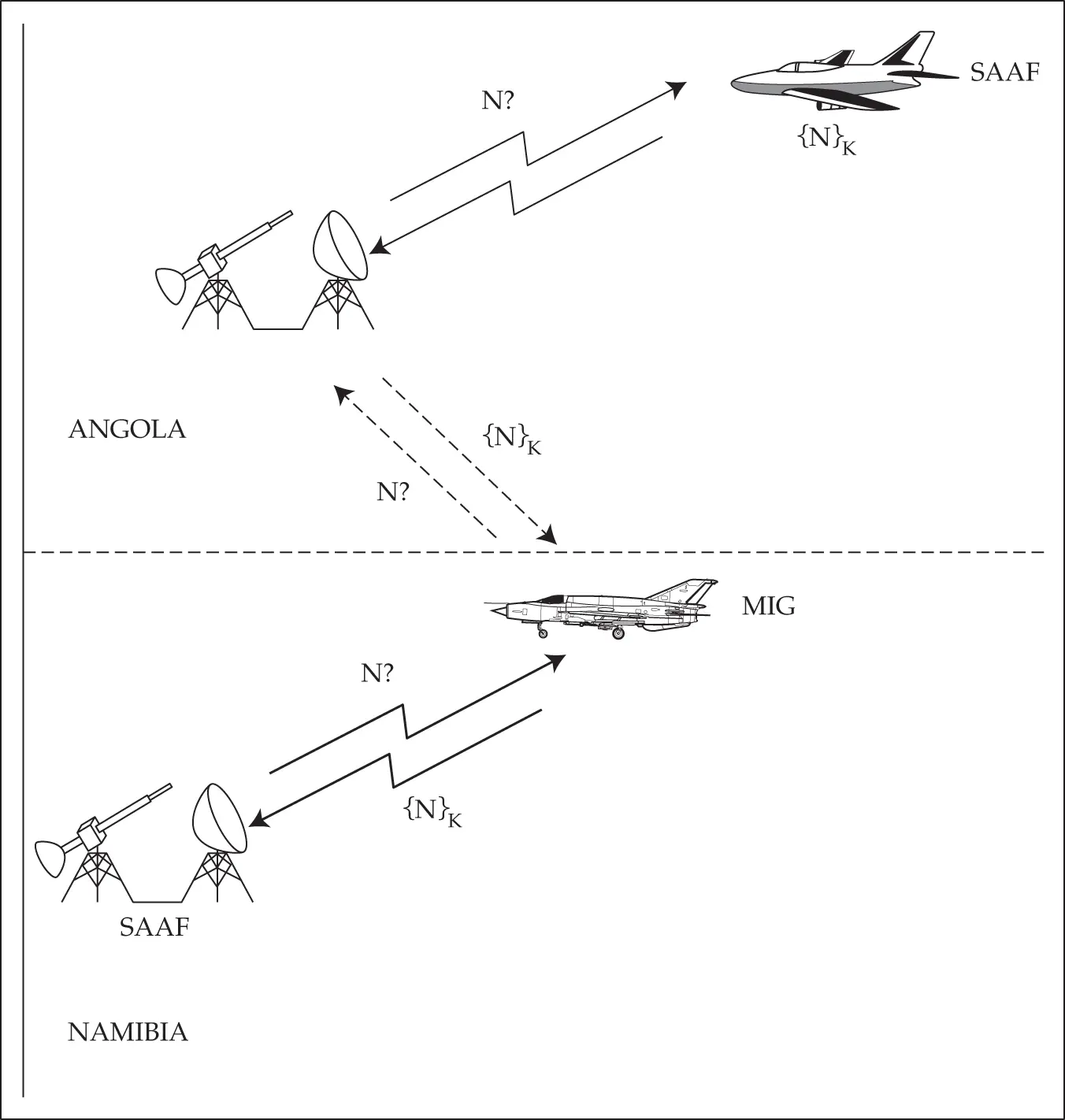
Figure 4.2 : The MIG-in-the middle attack
In any case, the tale gives us another illustration of the man-in-the-middle attack. The relay attack against cars is another example. It also works against password calculators: the phishing site invites the mark to log on and simultaneously opens a logon session with his bank. The bank sends a challenge; the phisherman relays this to the mark, who uses his device to respond to it; the phisherman relays the response to the bank, and the bank now accepts the phisherman as the mark.
Stopping a middleperson attack is harder than it looks, and may involve multiple layers of defence. Banks typically look for a known machine, a password, a second factor such as an authentication code from a CAP reader, and a risk assessment of the transaction. For high-risk transactions, such as adding a new payee to an account, both my banks demand that I compute an authentication code on the payee account number. But they only authenticate the last four digits, because of usability. If it takes two minutes and the entry of dozens of digits to make a payment, then a lot of customers will get digits wrong, give up, and then either call the call center or get annoyed and bank elsewhere. Also, the bad guys may be able to exploit any fallback mechanisms, perhaps by spoofing customers into calling phone numbers that run a middleperson attack between the customer and the call center. I'll discuss all this further in the chapter on Banking and Bookkeeping.
We will come across such attacks again and again in applications ranging from Internet security protocols to Bluetooth. They even apply in gaming. As the mathematician John Conway once remarked, it's easy to get at least a draw against a grandmaster at postal chess: just play two grandmasters at once, one as white and the other as black, and relay the moves between them!
Further interesting problems arise when two principals have to identify each other. Suppose that a challenge-response IFF system designed to prevent anti-aircraft gunners attacking friendly aircraft had to be deployed in a fighter-bomber too. Now suppose that the air force simply installed one of their air gunners' challenge units in each aircraft and connected it to the fire-control radar.
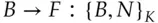
But now when a fighter challenges an enemy bomber, the bomber might just reflect the challenge back to the fighter's wingman, get a correct response, and then send that back as its own response:
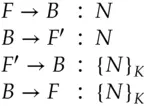
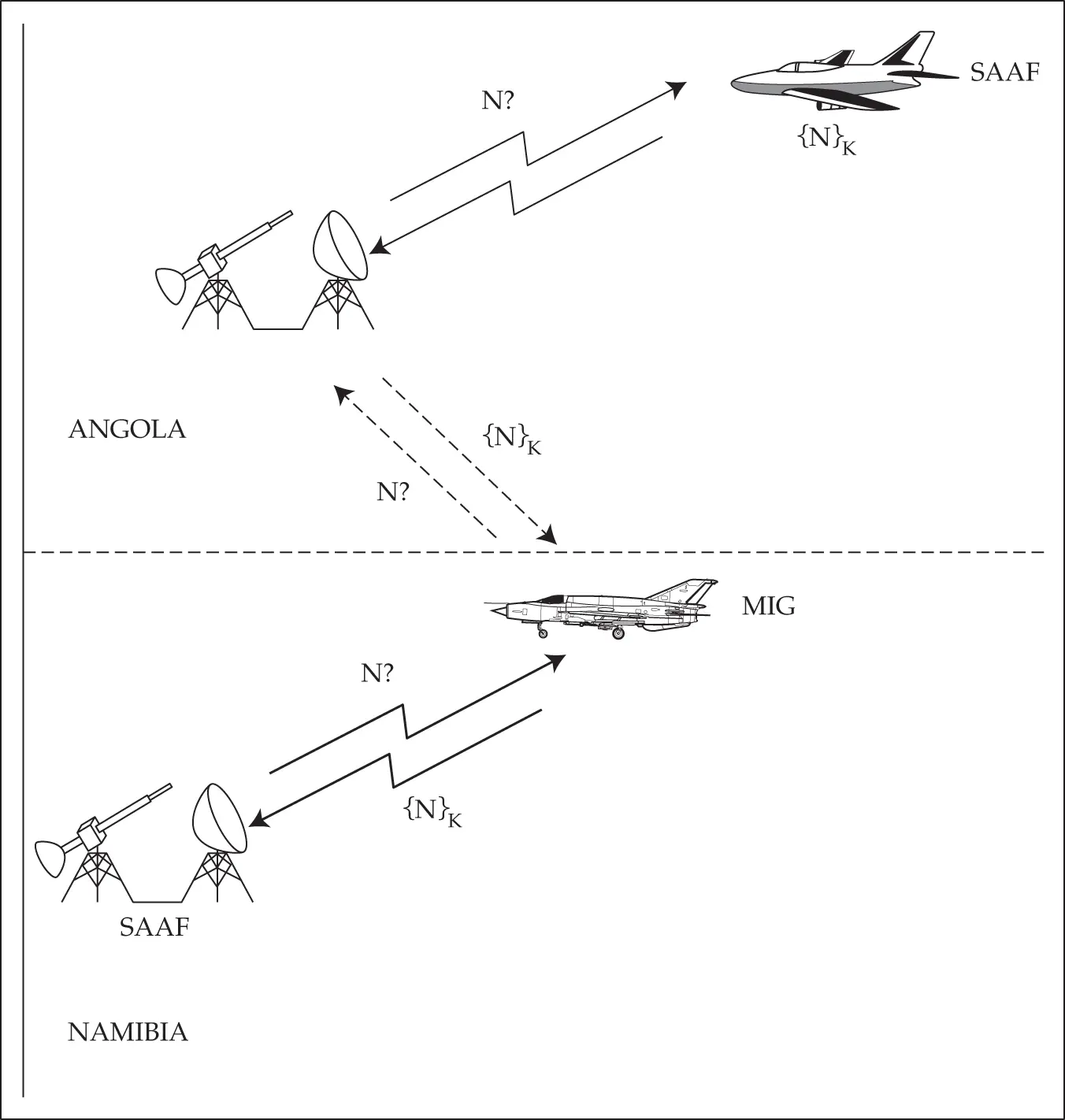
There are a number of ways of stopping this, such as including the names of the two parties in the exchange. In the above example, we might require a friendly bomber to reply to the challenge:

with a response such as:
Thus a reflected response  from the wingman
from the wingman  could be detected 5.
could be detected 5.
This serves to illustrate the subtlety of the trust assumptions that underlie authentication. If you send out a challenge  and receive, within 20 milliseconds, a response
and receive, within 20 milliseconds, a response  , then – since light can travel a bit under 3,730 miles in 20 ms – you know that there is someone with the key
, then – since light can travel a bit under 3,730 miles in 20 ms – you know that there is someone with the key  within 2000 miles. But that's all you know. If you can be sure that the response was not computed using your own equipment, you now know that there is someone else with the key
within 2000 miles. But that's all you know. If you can be sure that the response was not computed using your own equipment, you now know that there is someone else with the key  within two thousand miles. If you make the further assumption that all copies of the key
within two thousand miles. If you make the further assumption that all copies of the key  are securely held in equipment which may be trusted to operate properly, and you see
are securely held in equipment which may be trusted to operate properly, and you see  , you might be justified in deducing that the aircraft with callsign
, you might be justified in deducing that the aircraft with callsign  is within 2000 miles. A careful analysis of trust assumptions and their consequences is at the heart of security protocol design.
is within 2000 miles. A careful analysis of trust assumptions and their consequences is at the heart of security protocol design.
By now you might think that we understand all the protocol design aspects of IFF. But we've omitted one of the most important problems – and one which the designers of early IFF systems didn't anticipate. As radar is passive the returns are weak, while IFF is active and so the signal from an IFF transmitter will usually be audible at a much greater range than the same aircraft's radar return. The Allies learned this the hard way; in January 1944, decrypts of Enigma messages revealed that the Germans were plotting British and American bombers at twice the normal radar range by interrogating their IFF. So more modern systems authenticate the challenge as well as the response. The NATO mode XII, for example, has a 32 bit encrypted challenge, and a different valid challenge is generated for every interrogation signal, of which there are typically 250 per second. Theoretically there is no need to switch off over enemy territory, but in practice an enemy who can record valid challenges can replay them as part of an attack. Relays are made difficult in mode XII using directionality and time-of-flight.
Читать дальше


 from the wingman
from the wingman  could be detected 5.
could be detected 5. and receive, within 20 milliseconds, a response
and receive, within 20 milliseconds, a response  , then – since light can travel a bit under 3,730 miles in 20 ms – you know that there is someone with the key
, then – since light can travel a bit under 3,730 miles in 20 ms – you know that there is someone with the key  within 2000 miles. But that's all you know. If you can be sure that the response was not computed using your own equipment, you now know that there is someone else with the key
within 2000 miles. But that's all you know. If you can be sure that the response was not computed using your own equipment, you now know that there is someone else with the key  within two thousand miles. If you make the further assumption that all copies of the key
within two thousand miles. If you make the further assumption that all copies of the key  are securely held in equipment which may be trusted to operate properly, and you see
are securely held in equipment which may be trusted to operate properly, and you see  , you might be justified in deducing that the aircraft with callsign
, you might be justified in deducing that the aircraft with callsign  is within 2000 miles. A careful analysis of trust assumptions and their consequences is at the heart of security protocol design.
is within 2000 miles. A careful analysis of trust assumptions and their consequences is at the heart of security protocol design.









