Security has a wide base and addresses specific issues regarding computers, networks, communication devices, data, information, people, organizations, and governments. Users must have confidence that information systems operate as intended without unanticipated failures or problems. Also, users must have confidence that information is handled timely, accurately, confidentially, and reliably.
Following this document [OECD 2002], OECD published more technical guidelines and recommendations for the implementation and management of security [OECD 2003], [USCIB 2004], [OECD 2005], [OECD 2008] including privacy [OECD 2016]. Revisions of the guidelines are reported in [OECD 2012a], [OECD 2012c].
On 17 September 2015 the OECD Council adopted the Recommendation on Digital Security Risk Management [OECD 2015], which replaces the 2002 guidelines. The [OECD 2015] document provides guidance for a new generation of national strategies on the management of digital security risk aimed to optimize the economic and social benefits expected from digital openness. The recommendation calls on governments, public, and private organizations to adopt an approach to digital security risk management that builds trust and takes advantage of the open digital environment for economic and social prosperity. As described in this document, digital security implies that security is approached from at least four different perspectives, each stemming from a different culture and background, recognized practices, and objectives:
Technology that is focusing on the functioning of the digital environment (often called information security, computer security, or network security by experts).
Law enforcement and, more generally, legal aspects (e.g. cybercrime).
National and international security, including aspects such as the role of information and communication technologies (ICTs) with respect to intelligence, conflict prevention, warfare, etc.
Economic and social prosperity, encompassing wealth creation, innovation, growth, competitiveness, and employment across all economic sectors, as well as aspects such as individual liberties, health, education, culture, democratic participation, science, and other dimensions of well‐being in which the digital environment is driving progress.
The continuous growth of cybersecurity threats and attacks including the increasing sophistication of the malware is impacting the security of energy sector and other critical infrastructures. The energy industry includes electricity sector that provides the production and delivery of power to consumers through a grid connection.
Currently, cybersecurity is a widespread and growing concern for the energy sector. In addition, the energy market shows the presence of emerging Smart Grid phenomena, which introduce new security concerns. In the context of this book, security has a wide base and addresses specific issues regarding power grid and Smart Grid with its related technologies such as Internet of things, cyber–physical systems, industrial control systems, communication networks, computers, information, organization, and people, and others.
The Smart Grid is evolving from the traditional electrical grid. An electrical grid (also referred to as an electricity grid or electric grid) is an interconnected network for delivering electricity from suppliers to consumers. It consists of generating stations that produce electrical power, high‐voltage transmission lines that carry power from distant sources to demand centers, and distribution lines that connect individual customers. The US electric power system has provided highly reliable electricity for more than a century.
1.2.1 Traditional Power Grid Architecture
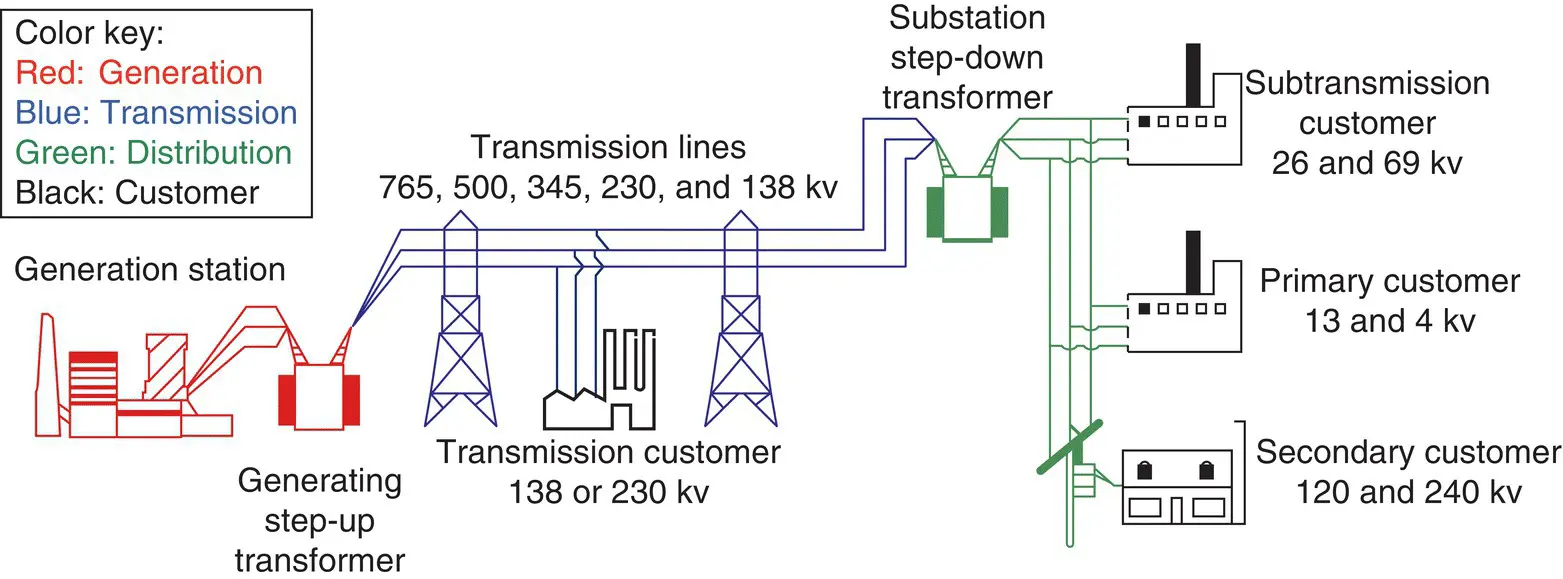
The traditional architecture (see Figure 1.1) is based on large‐scale generation remotely located from consumers, hierarchical control structures with minimal feedback, limited energy storage, one‐way control, and passive loads.
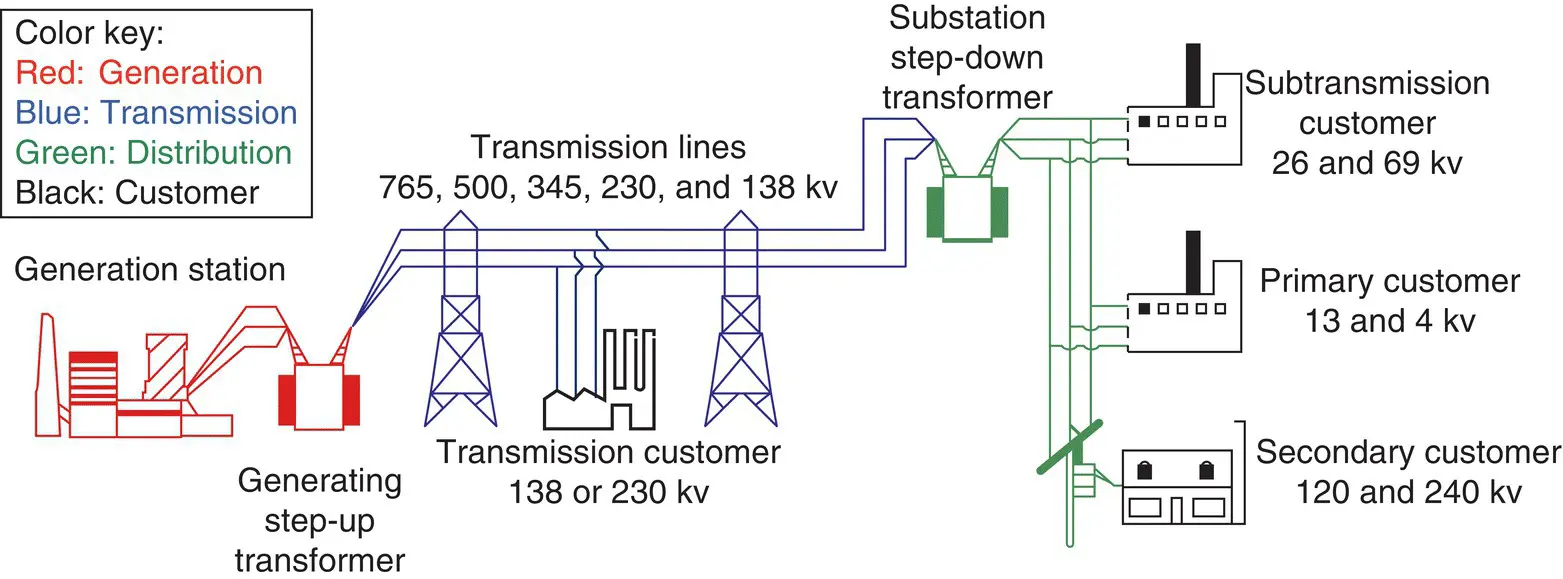
Figure 1.1 Traditional electricity delivery system.
Source: [DOE 2015a]. Public Domain.
As illustrated in Figure 1.1, the electricity sector is composed of four distinct functions: generation, transmission, distribution, and system operations. Once electricity is generated, it is generally sent through high‐voltage, high‐capacity transmission lines to local electricity distributors. Once there, electricity is transformed into a lower voltage and sent through local distribution lines for consumption by industrial plants, businesses, and residential consumers.
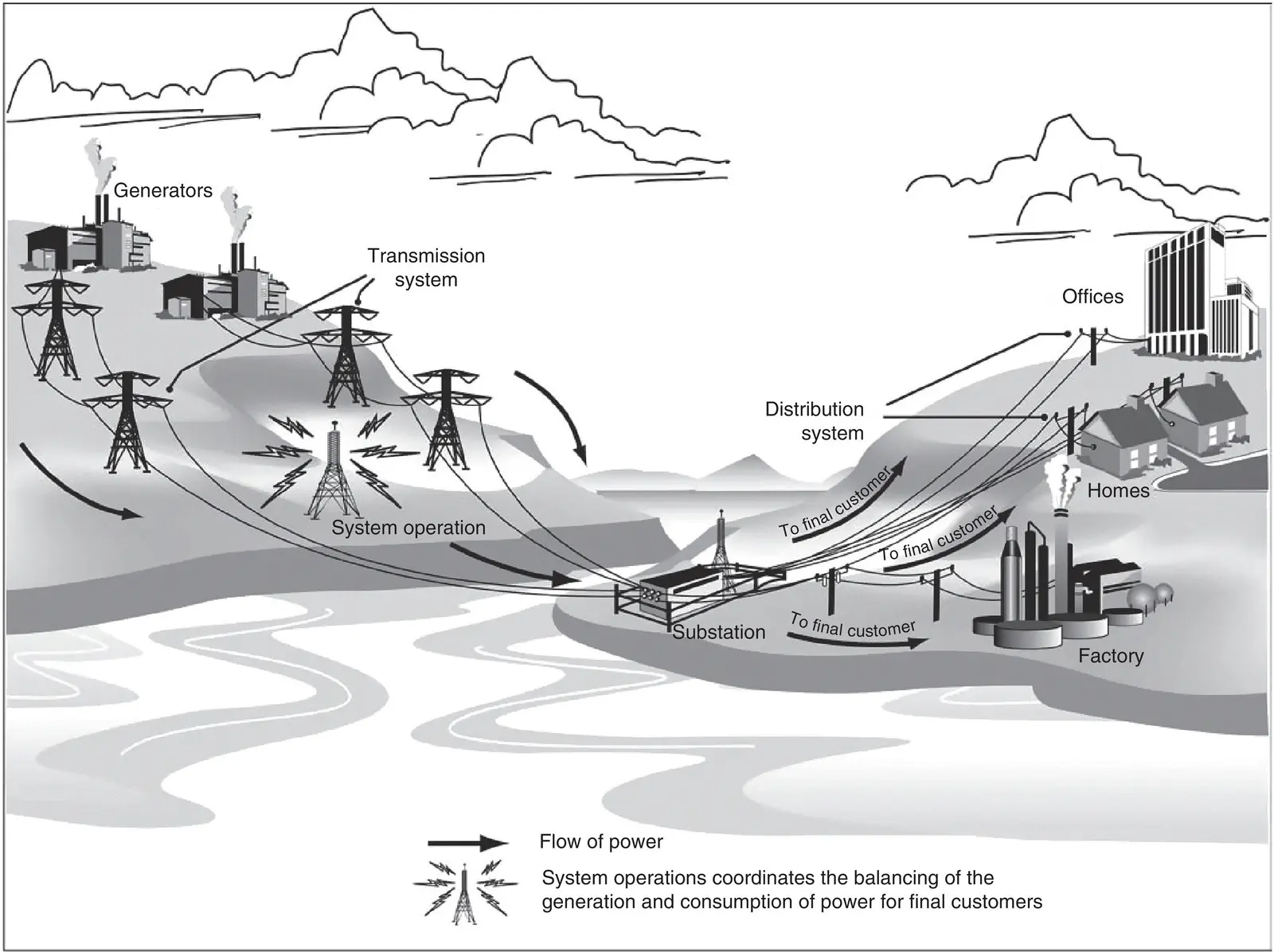
Because electric energy is generated and consumed almost instantaneously, the operation of an electric power system requires that a system operator constantly balance the generation and consumption of power. Figure 1.2shows additional functional systems (transmission system, system operations, distribution system) and substation connected to different customers (offices, residential customers, and industrial customers). Information including basic definitions of terms and concepts related to the electrical power grid can be also found in the references and glossaries included in Appendix B.
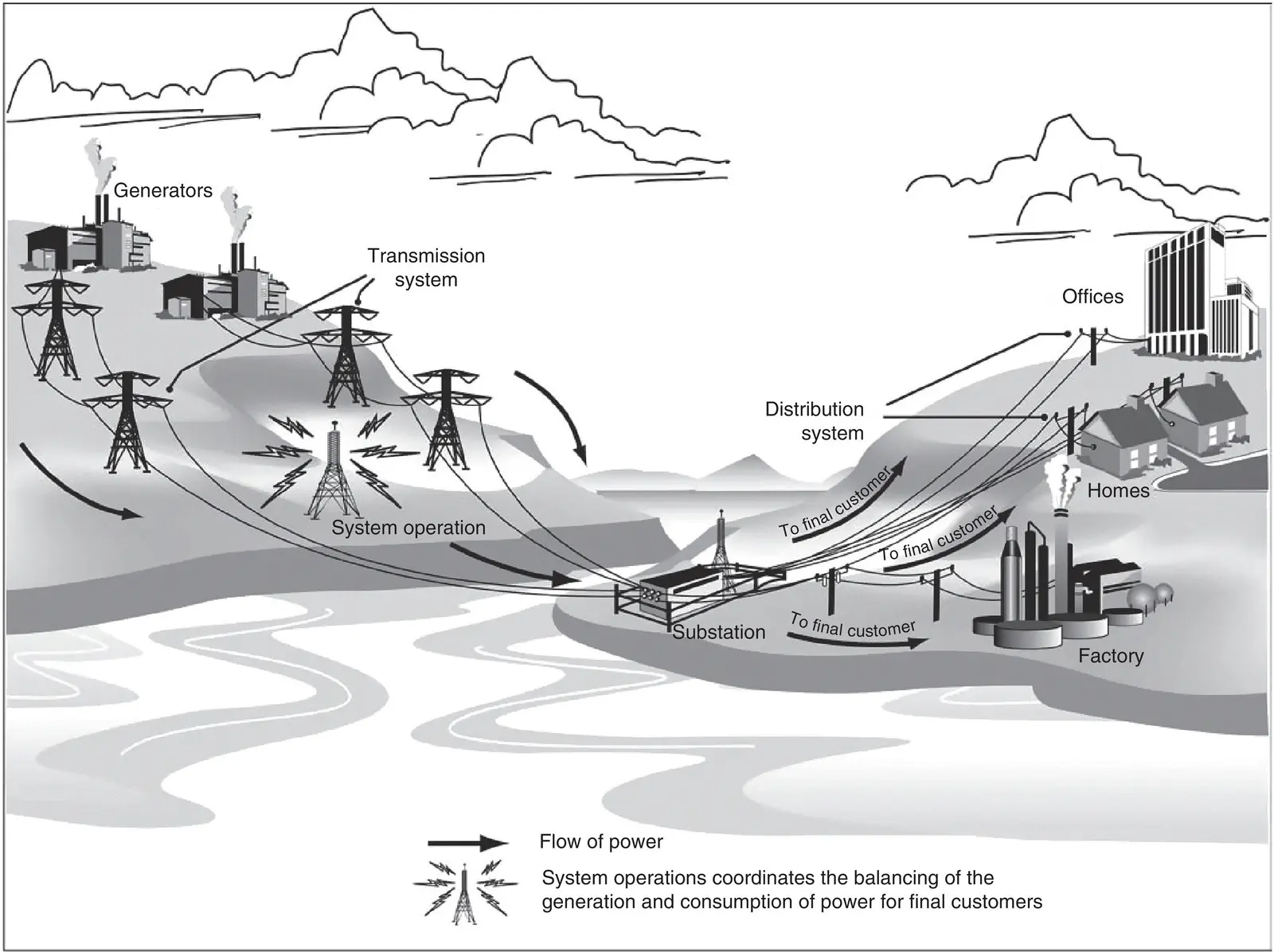
Figure 1.2 Functions of the electricity sector.
Source: [GAO 2011]. Public Domain.
In the US electric sector, the key players include utilities and system operators [GAO 2011]:
Utilities own and operate electricity assets, which may include generation plants, transmission lines, distribution lines, and substations including structures often seen in residential and commercial areas that contain technical equipment such as switches and transformers to ensure smooth, safe flow of current and voltage. Utilities may be owned by investors, municipalities, and individuals (as in cooperative utilities).
System operators are sometimes affiliated with a particular utility or sometimes independent and responsible for managing the electricity flows in multiple utility areas. The system operators manage and control the generation, transmission, and distribution of electric power using control systems, IT information systems, and network‐based systems that monitor and control sensitive processes and physical functions, including opening and closing circuit breakers (see definitions in Appendix B). Therefore, the effective functioning of the electricity industry is highly dependent on these control systems.
However, for many years, the US electricity network lacked opportunities such as [GAO 2011]:
Adequate technologies (e.g. sensors) to allow system operators to monitor how much electricity was flowing on distribution lines.
Communication networks to further integrate parts of the electricity grid with control centers.
Computerized control devices to automate system management and recovery.
1.2.1.2 Electric Grid Design of the Future
As the electric grid transitions from the traditional design to the design of the future, new features and technologies must be incorporated. Increasing communications and computing capabilities are transforming power grid from the traditional centralized model to an integrated hybrid centralized/decentralized system. Therefore, society and the power industry in particular are challenged by the transformation of the power grid, as introduced by Nikola Tesla about 120 years ago, into a Smart Grid.
Читать дальше