Security is a journey, not a finish line. It is not a process that will ever be concluded. It is not possible to fully secure something, because security issues are always changing. Our deployed technology is changing by the passage of time, by the users, and by the adversaries discovering flaws and developing exploits. The defenses that were sufficient yesterday may not be sufficient tomorrow. As new vulnerabilities are discovered, as new means of attack are crafted and new exploits are built, we have to respond by reassessing our security infrastructure and responding appropriately.
Understand and Apply Security Concepts
Security management concepts and principles are inherent elements in a security policy and solution deployment. They define the basic parameters needed for a secure environment. They also define the goals and objectives that both policy designers and system implementers must achieve to create a secure solution.
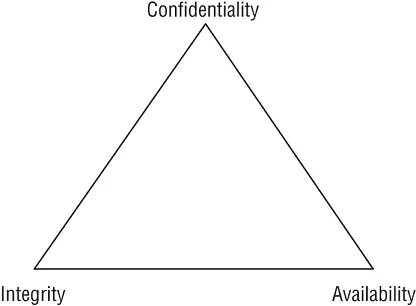
Confidentiality, integrity, and availability (CIA) (i.e., the CIA Triad ) are typically viewed as the primary goals and objectives of a security infrastructure (see Figure 1.1).
FIGURE 1.1The CIA Triad
Security controls are typically evaluated on how well they address these three core information security tenets. Vulnerabilities and risks are also evaluated based on the threat they pose against one or more of the CIA Triad principles.
The first principle of the CIA Triad is confidentiality. Confidentiality is the concept of the measures used to ensure the protection of the secrecy of data, objects, or resources. The goal of confidentiality protection is to prevent or minimize unauthorized access to data. Confidentiality protections prevent disclosure while protecting authorized access.
Violations of confidentiality are not limited to directed intentional attacks. Many instances of unauthorized disclosure of sensitive or confidential information are the result of human error, oversight, or ineptitude. Confidentiality violations can result from the actions of an end user or a system administrator. They can also occur because of an oversight in a security policy or a misconfigured security control.
Numerous countermeasures can help ensure confidentiality against possible threats. These include encryption, network traffic padding, strict access control, rigorous authentication procedures, data classification, and extensive personnel training.
Concepts, conditions, and aspects of confidentiality include the following:
Sensitivity Sensitivity refers to the quality of information, which could cause harm or damage if disclosed.
Discretion Discretion is an act of decision where an operator can influence or control disclosure in order to minimize harm or damage.
Criticality The level to which information is mission critical is its measure of criticality. The higher the level of criticality, the more likely the need to maintain the confidentiality of the information.
Concealment Concealment is the act of hiding or preventing disclosure. Often concealment is viewed as a means of cover, obfuscation, or distraction. A related concept to concealment is security through obscurity, which is the concept of attempting to gain protection through hiding, silence, or secrecy.
Secrecy Secrecy is the act of keeping something a secret or preventing the disclosure of information.
Privacy Privacy refers to keeping information confidential that is personally identifiable or that might cause harm, embarrassment, or disgrace to someone if revealed.
Seclusion Seclusion involves storing something in an out-of-the-way location, likely with strict access controls.
Isolation Isolation is the act of keeping something separated from others.
Organizations should evaluate the nuances of confidentiality they wish to enforce. Tools and technology that implement one form of confidentiality might not support or allow other forms.
Integrity is the concept of protecting the reliability and correctness of data. Integrity protection prevents unauthorized alterations of data. Properly implemented integrity protection provides a means for authorized changes while protecting against intended and malicious unauthorized activities (such as viruses and intrusions) as well as mistakes made by authorized users (such as accidents or oversights).
Integrity can be examined from three perspectives:
Preventing unauthorized subjects from making modifications
Preventing authorized subjects from making unauthorized modifications, such as mistakes
Maintaining the internal and external consistency of objects so that their data is a correct and true reflection of the real world and any relationship with any other object is valid, consistent, and verifiable
For integrity to be maintained on a system, controls must be in place to restrict access to data, objects, and resources. Maintaining and validating object integrity across storage, transport, and processing requires numerous variations of controls and oversight.
Numerous attacks focus on the violation of integrity. These include viruses, logic bombs, unauthorized access, errors in coding and applications, malicious modification, intentional replacement, and system backdoors.
Human error, oversight, or ineptitude accounts for many instances of unauthorized alteration of sensitive information. They can also occur because of an oversight in a security policy or a misconfigured security control.
Numerous countermeasures can ensure integrity against possible threats. These include strict access control, rigorous authentication procedures, intrusion detection systems, object/data encryption, hash verifications (see Chapter 6, “Cryptography and Symmetric Key Algorithms,” and Chapter 7, “PKI and Cryptographic Applications”), interface restrictions, input/function checks, and extensive personnel training.
Confidentiality and integrity depend on each other. Without object integrity (in other words, the inability of an object to be modified without permission), confidentiality cannot be maintained.
Integrity is dependent on confidentiality and access control. Concepts, conditions, and aspects of integrity include the following:
Accuracy: Being correct and precise
Truthfulness: Being a true reflection of reality
Validity: Being factually or logically sound
Accountability: Being responsible or obligated for actions and results
Responsibility: Being in charge or having control over something or someone
Completeness: Having all necessary components or parts
Comprehensiveness: Being complete in scope; the full inclusion of all needed elements
Availability means authorized subjects are granted timely and uninterrupted access to objects. Often, availability protection controls support sufficient bandwidth and timeliness of processing as deemed necessary by the organization or situation. Availability includes efficient uninterrupted access to objects and prevention of denial-of-service (DoS) attacks. Availability also implies that the supporting infrastructure—including network services, communications, and access control mechanisms—is functional and allows authorized users to gain authorized access.
For availability to be maintained on a system, controls must be in place to ensure authorized access and an acceptable level of performance, to quickly handle interruptions, provide for redundancy, maintain reliable backups, and prevent data loss or destruction.
Читать дальше