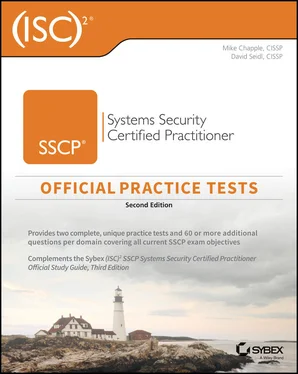
Mike Chapple - (ISC)2 SSCP Systems Security Certified Practitioner Official Practice Tests
Здесь есть возможность читать онлайн «Mike Chapple - (ISC)2 SSCP Systems Security Certified Practitioner Official Practice Tests» — ознакомительный отрывок электронной книги совершенно бесплатно, а после прочтения отрывка купить полную версию. В некоторых случаях можно слушать аудио, скачать через торрент в формате fb2 и присутствует краткое содержание. Жанр: unrecognised, на английском языке. Описание произведения, (предисловие) а так же отзывы посетителей доступны на портале библиотеки ЛибКат.
- Название:(ISC)2 SSCP Systems Security Certified Practitioner Official Practice Tests
- Автор:
- Жанр:
- Год:неизвестен
- ISBN:нет данных
- Рейтинг книги:3 / 5. Голосов: 1
-
Избранное:Добавить в избранное
- Отзывы:
-
Ваша оценка:
- 60
- 1
- 2
- 3
- 4
- 5
(ISC)2 SSCP Systems Security Certified Practitioner Official Practice Tests: краткое содержание, описание и аннотация
Предлагаем к чтению аннотацию, описание, краткое содержание или предисловие (зависит от того, что написал сам автор книги «(ISC)2 SSCP Systems Security Certified Practitioner Official Practice Tests»). Если вы не нашли необходимую информацию о книге — напишите в комментариях, мы постараемся отыскать её.
(ISC)² SSCP Official Practice Tests, 2nd Edition
(ISC)2 SSCP Systems Security Certified Practitioner Official Practice Tests — читать онлайн ознакомительный отрывок
Ниже представлен текст книги, разбитый по страницам. Система сохранения места последней прочитанной страницы, позволяет с удобством читать онлайн бесплатно книгу «(ISC)2 SSCP Systems Security Certified Practitioner Official Practice Tests», без необходимости каждый раз заново искать на чём Вы остановились. Поставьте закладку, и сможете в любой момент перейти на страницу, на которой закончили чтение.
Интервал:
Закладка:
8 During a log review, Danielle discovers a series of logs that show login failures.Jan 31 11:39:12 ip-10-0-0-2 sshd[29092]: Invalid user admin from remotehost passwd=aaaaaaaa Jan 31 11:39:20 ip-10-0-0-2 sshd[29098]: Invalid user admin from remotehost passwd=aaaaaaab Jan 31 11:39:23 ip-10-0-0-2 sshd[29100]: Invalid user admin from remotehost passwd=aaaaaaac Jan 31 11:39:31 ip-10-0-0-2 sshd[29106]: Invalid user admin from remotehost passwd=aaaaaaad Jan 31 20:40:53 ip-10-0-0-254 sshd[30520]: Invalid user admin from remotehost passwd=aaaaaaaeWhat type of attack has Danielle discovered?A pass-the-hash attackA brute-force attackA man-in-the-middle attackA dictionary attack
9 During a third-party audit, Jim’s company receives a finding that states, “The administrator should review backup success and failure logs on a daily basis, and take action in a timely manner to resolve reported exceptions.” What is the biggest issue that is likely to result if Jim’s IT staff need to restore from a backup?They will not know if the backups succeeded or failed.The backups may not be properly logged.The backups may not be usable.The backup logs may not be properly reviewed.
For questions 39–41, please refer to the following scenario.
Ben’s organization has begun to use STRIDE to assess its software and has identified threat agents and the business impacts that these threats could have. Now they are working to identify appropriate controls for the issues they have identified.
1 Ben’s development team needs to address an authorization issue, resulting in an elevation of privilege threat. Which of the following controls is most appropriate to this type of issue?Auditing and logging are enabled.Role-based access control is used for specific operations.Data type and format checks are enabled.User input is tested against a whitelist.
2 Ben’s team is attempting to categorize a transaction identification issue that is caused by use of a symmetric key shared by multiple servers. What STRIDE category should this fall into?Information disclosureDenial of serviceTamperingRepudiation
3 Ben wants to prevent or detect tampering with data. Which of the following is not an appropriate solution?HashesDigital signaturesFilteringAuthorization controls
4 During a port scan of his network, Alex finds that a number of hosts respond on TCP ports 80, 443, 515, and 9100 in offices throughout his organization. What type of devices is Alex likely discovering?Web serversFile serversWireless access pointsPrinters
5 Alan is performing threat modeling and decides that it would be useful to decompose the system into the key elements shown here. What tool is he using?Image reprinted from CISSP (ISC)2 Certified Information Systems Security Professional Official Study Guide, 7th Edition © John Wiley & Sons 2015, reprinted with permission.Vulnerability assessmentFuzzingReduction analysisData modeling
6 Which of the following is not a hazard associated with penetration testing?Application crashesDenial of serviceExploitation of vulnerabilitiesData corruption
7 Nmap is an example of what type of tool?Vulnerability scannerWeb application fuzzerNetwork design and layoutPort scanner
8 Which of the following is a method used to design new software tests and to ensure the quality of tests?Code auditingStatic code analysisRegression testingMutation testing
9 When a Windows system is rebooted, what type of log is generated?ErrorWarningInformationFailure audit
10 What is the first step that should occur before a penetration test is performed?Data gatheringPort scanningGetting permissionPlanning
11 Bobbi is investigating a security incident and discovers that an attacker began with a normal user account but managed to exploit a system vulnerability to provide that account with administrative rights. What type of attack took place under the STRIDE threat model?SpoofingRepudiationTamperingElevation of privilege
For questions 50–53, please refer to the following scenario.
Ann is a security professional for a midsize business and typically handles log analysis and security monitoring tasks for her organization. One of her roles is to monitor alerts originating from the organization’s intrusion detection system. The system typically generates several dozen alerts each day, and many of those alerts turn out to be false alarms after her investigation.
This morning, the intrusion detection system alerted because the network began to receive an unusually high volume of inbound traffic. Ann received this alert and began looking into the origin of the traffic.
1 At this point in the incident response process, what term best describes what has occurred in Ann’s organization?Security occurrenceSecurity incidentSecurity eventSecurity intrusion
2 Ann continues her investigation and realizes that the traffic generating the alert is abnormally high volumes of inbound UDP traffic on port 53. What service typically uses this port?DNSSSH/SCPSSL/TLSHTTP
3 As Ann analyzes the traffic further, she realizes that the traffic is coming from many different sources and has overwhelmed the network, preventing legitimate uses. The inbound packets are responses to queries that she does not see in outbound traffic. The responses are abnormally large for their type. What type of attack should Ann suspect?ReconnaissanceMalicious codeSystem penetrationDenial of service
4 Now that Ann understands that an attack has taken place that violates her organization’s security policy, what term best describes what has occurred in Ann’s organization?Security occurrenceSecurity incidentSecurity eventSecurity intrusion
5 During a log review, Saria discovers a series of logs that show login failures, as shown here:Jan 31 11:39:12 ip-10-0-0-2 sshd[29092]: Invalid user admin from remotehost passwd=orange Jan 31 11:39:20 ip-10-0-0-2 sshd[29098]: Invalid user admin from remotehost passwd=Orang3 Jan 31 11:39:23 ip-10-0-0-2 sshd[29100]: Invalid user admin from remotehost passwd=Orange93 Jan 31 11:39:31 ip-10-0-0-2 sshd[29106]: Invalid user admin from remotehost passwd=Orangutan1 Jan 31 20:40:53 ip-10-0-0-254 sshd[30520]: Invalid user admin from remotehost passwd=OrangemonkeyWhat type of attack has Saria discovered?A brute-force attackA man-in-the-middle attackA dictionary attackA rainbow table attack
6 Ben is seeking a control objective framework that is widely accepted around the world and focuses specifically on information security controls. Which one of the following frameworks would best meet his needs?ITILISO 27002CMMPMBOK Guide
7 Alex is using nmap to perform port scanning of a system, and he receives three different port status messages in the results. Match each of the numbered status messages with the appropriate lettered description. You should use each item exactly once.Status messageOpenClosedFilteredDescriptionThe port is accessible on the remote system, but no application is accepting connections on that port.The port is not accessible on the remote system.The port is accessible on the remote system, and an application is accepting connections on that port.
8 Tony is developing a business continuity plan and is having difficulty prioritizing resources because of the difficulty of combining information about tangible and intangible assets. What would be the most effective risk assessment approach for him to use?Quantitative risk assessmentQualitative risk assessmentNeither quantitative nor qualitative risk assessmentCombination of quantitative and qualitative risk assessment
9 Angela wants to test a web browser’s handling of unexpected data using an automated tool. What tool should she choose?NmapzzufNessusNikto
10 Saria wants to log and review traffic information between parts of her network. What type of network logging should she enable on her routers to allow her to perform this analysis?Audit loggingFlow loggingTrace loggingRoute logging
Читать дальшеИнтервал:
Закладка:
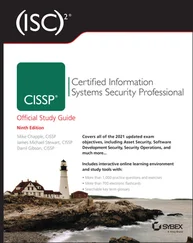
Похожие книги на «(ISC)2 SSCP Systems Security Certified Practitioner Official Practice Tests»
Представляем Вашему вниманию похожие книги на «(ISC)2 SSCP Systems Security Certified Practitioner Official Practice Tests» списком для выбора. Мы отобрали схожую по названию и смыслу литературу в надежде предоставить читателям больше вариантов отыскать новые, интересные, ещё непрочитанные произведения.
Обсуждение, отзывы о книге «(ISC)2 SSCP Systems Security Certified Practitioner Official Practice Tests» и просто собственные мнения читателей. Оставьте ваши комментарии, напишите, что Вы думаете о произведении, его смысле или главных героях. Укажите что конкретно понравилось, а что нет, и почему Вы так считаете.