Stephen Winters-Hilt - Informatics and Machine Learning
Здесь есть возможность читать онлайн «Stephen Winters-Hilt - Informatics and Machine Learning» — ознакомительный отрывок электронной книги совершенно бесплатно, а после прочтения отрывка купить полную версию. В некоторых случаях можно слушать аудио, скачать через торрент в формате fb2 и присутствует краткое содержание. Жанр: unrecognised, на английском языке. Описание произведения, (предисловие) а так же отзывы посетителей доступны на портале библиотеки ЛибКат.
- Название:Informatics and Machine Learning
- Автор:
- Жанр:
- Год:неизвестен
- ISBN:нет данных
- Рейтинг книги:3 / 5. Голосов: 1
-
Избранное:Добавить в избранное
- Отзывы:
-
Ваша оценка:
- 60
- 1
- 2
- 3
- 4
- 5
Informatics and Machine Learning: краткое содержание, описание и аннотация
Предлагаем к чтению аннотацию, описание, краткое содержание или предисловие (зависит от того, что написал сам автор книги «Informatics and Machine Learning»). Если вы не нашли необходимую информацию о книге — напишите в комментариях, мы постараемся отыскать её.
Discover a thorough exploration of how to use computational, algorithmic, statistical, and informatics methods to analyze digital data Informatics and Machine Learning: From Martingales to Metaheuristics
ad hoc, ab initio
Informatics and Machine Learning: From Martingales to Metaheuristics
Informatics and Machine Learning — читать онлайн ознакомительный отрывок
Ниже представлен текст книги, разбитый по страницам. Система сохранения места последней прочитанной страницы, позволяет с удобством читать онлайн бесплатно книгу «Informatics and Machine Learning», без необходимости каждый раз заново искать на чём Вы остановились. Поставьте закладку, и сможете в любой момент перейти на страницу, на которой закончили чтение.
Интервал:
Закладка:
5 Chapter 6Figure 6.1 The most common stochastic sequential analysis flow topology. The...Figure 6.2 Graphical model for a first‐order Markov model.Figure 6.3 Graphical model for a standard hidden Markov model.Figure 6.4 The most probable state sequence.Figure 6.5 Viterbi path. Optimal path identification.Figure 6.6 Comparison of standard HMM and the clique‐generalized HMM. The up...Figure 6.7 HMM/EM Viterbi‐path level occupation feature extraction. Strong E...Figure 6.8 The binary classification performance using features extracted wi...Figure 6.9 Adaboost feature selection strengthens the SVM performance of the...Figure 6.10 If Adaboost operates from the 150 component manual set, a reduce...Figure 6.11 AdaBoosting to select 100 of the full set of 2600 features impro...
6 Chapter 7Figure 7.1 Top Panel. Sliding‐window association (clique) of observations an...Figure 7.2 The transition schematic for the HMM with duration (HMMD).Figure 7.3 Viterbi column‐pointer match de‐segmentation rule. Table 1 and Ta...
7 Chapter 8Figure 8.1 Map.Figure 8.2 Chart.Figure 8.3 Overlapping charts.Figure 8.4 Curve. Note: The parameterization λ defines different curves...Figure 8.5 Function.Figure 8.6 Tangent Bundle, where “cross‐section” of TM (gives intuitive noti...Figure 8.7 1 Forms and cotangent bundle. There is a duality between 1 forms ...Figure 8.8 Gradient 1 form.Figure 8.9 Parallel transport.
8 Chapter 9Figure 9.1 Single Neuron with step (threshold) activation function. The inpu...Figure 9.2 Perceptron update. The update rule shifts the position of the sep...Figure 9.3 Single Neuron, Sigma activation function: the inputs x kare multi...Figure 9.4 Neural Net, layered topology, fully connected between layers (“de...Figure 9.5 Link functions for GD (linear), EGU +/−(left and right curv...Figure 9.6 Link functions for BEG (sigmoid curve), where f ( ω ) =  , L <
, L <
9 Chapter 10Figure 10.1 Supervised learning: separability and maximum margin. Shown in t...Figure 10.2 Support vectors on margin boundary.Figure 10.3 (Left) One of the former positives (central to the positive clus...Figure 10.4 Separable solution with maximum width margin.Figure 10.5 Post‐training, have decision hyperplane. Now test data (ci...Figure 10.6 Two clusters, roughly, shown, with intra‐cluster distance shown ...Figure 10.7 Schematic for SVM‐based clustering, starting with randomly label...Figure 10.8 Sum of squared error (SSE) scoring. SSE, the total of the sum of...Figure 10.9 Perceptron update. The update rule shifts the position of the se...Figure 10.10 Decision boundary (solid line); with margin (region between dot...Figure 10.11 The solid circle is the decision boundary. In the implementatio...Figure 10.12 A possible modeling configuration for two‐cluster explicit situ...Figure 10.13 The Hoeffding inequality can be reduced to P [∣ν − μ ∣ > ɛ ...Figure 10.14 Line Ax + By + C = 0 and a nearby point. D = 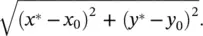 Figure 10.15 Hyperplane separability.
Figure 10.15 Hyperplane separability. 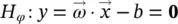 .Figure 10.16 IF C > α i, σ i→ ∅ ; If C = α i, σ ifree(≥∅)...Figure 10.17 Comparative results are shown on performance of Kernels and alg...Figure 10.18 SVM convergence failure seen with 100% SV passing on distribute...Figure 10.19 Sequential learning topology SV pass‐tuning. Dataset = 9G...Figure 10.20 Distributed learning topology SV pass‐tuning. Dataset = 9...Figure 10.21 SMO (non‐chunking) support vector reduction. Dataset: 9GC...Figure 10.22 Sequential chunking support vector reduction. Dataset: 9GC9CG_9...Figure 10.23 Multi‐threaded chunking support vector reduction. Dataset...Figure 10.24 Decision boundary (solid line); with margin (region between dot...Figure 10.25 Nanopore detector signal analysis architecture, with use of an ...Figure 10.26 The percentage data rejection vs. SN + SP curves are shown for ...Figure 10.27 The percentage data rejection vs. SN + SP curves are shown for ...Figure 10.28 The percent increase in iterations‐to‐convergence against the “Figure 10.29 The number of bounded support vectors (BSV) as a function of “ C Figure 10.30 (enlarged version of Figure 10.7) SVM‐external clustering metho...Figure 10.31 Summary of the degradation in clustering performance for less o...Figure 10.32 Efforts to use simulated annealing in the number of KKT violato...Figure 10.33 The results of SVM‐relabeler algorithm using a third degree pol...Figure 10.34 SVM‐external clustering results. (a) and (b) show the boost in ...Figure 10.35 The result of relabeler algorithm with perturbation. The top pl...Figure 10.36 (a, b) represent the SSE and purity evaluation of hybrid Re‐lab...Figure 10.37 Clustering performance comparisons: SVM‐external clustering com...Figure 10.38 Nanopore feature vector data (in standard 150 component, L 1‐nor...Figure 10.39 (a) Simulated annealing with constant perturbation, (b) simulat...Figure 10.40 Multiple‐convergence, SVM‐external clustering. Three multiple c...
.Figure 10.16 IF C > α i, σ i→ ∅ ; If C = α i, σ ifree(≥∅)...Figure 10.17 Comparative results are shown on performance of Kernels and alg...Figure 10.18 SVM convergence failure seen with 100% SV passing on distribute...Figure 10.19 Sequential learning topology SV pass‐tuning. Dataset = 9G...Figure 10.20 Distributed learning topology SV pass‐tuning. Dataset = 9...Figure 10.21 SMO (non‐chunking) support vector reduction. Dataset: 9GC...Figure 10.22 Sequential chunking support vector reduction. Dataset: 9GC9CG_9...Figure 10.23 Multi‐threaded chunking support vector reduction. Dataset...Figure 10.24 Decision boundary (solid line); with margin (region between dot...Figure 10.25 Nanopore detector signal analysis architecture, with use of an ...Figure 10.26 The percentage data rejection vs. SN + SP curves are shown for ...Figure 10.27 The percentage data rejection vs. SN + SP curves are shown for ...Figure 10.28 The percent increase in iterations‐to‐convergence against the “Figure 10.29 The number of bounded support vectors (BSV) as a function of “ C Figure 10.30 (enlarged version of Figure 10.7) SVM‐external clustering metho...Figure 10.31 Summary of the degradation in clustering performance for less o...Figure 10.32 Efforts to use simulated annealing in the number of KKT violato...Figure 10.33 The results of SVM‐relabeler algorithm using a third degree pol...Figure 10.34 SVM‐external clustering results. (a) and (b) show the boost in ...Figure 10.35 The result of relabeler algorithm with perturbation. The top pl...Figure 10.36 (a, b) represent the SSE and purity evaluation of hybrid Re‐lab...Figure 10.37 Clustering performance comparisons: SVM‐external clustering com...Figure 10.38 Nanopore feature vector data (in standard 150 component, L 1‐nor...Figure 10.39 (a) Simulated annealing with constant perturbation, (b) simulat...Figure 10.40 Multiple‐convergence, SVM‐external clustering. Three multiple c...
10 Chapter 11Figure 11.1 Gradient Ascent, Newton’s Ascent, Newton’s Ascent with restart....Figure 11.2 Metaheuristic #1: Euler’s Method – first‐order gradient ascent....Figure 11.3 Metaheuristic #2: Newton’s Method – second‐order gradient ascent...Figure 11.4 Metaheuristic #3: Newton’s Method – second‐order gradient ascent...Figure 11.5 Metaheuristic #4: (blind) hill climbing.Figure 11.6 Metaheuristic #5: steepest ascent hill climbing.Figure 11.7 Metaheuristic #6: steepest ascent hill climbing with restart.Figure 11.8 Metaheuristic #7: simulated annealing hill climbing.Figure 11.9 Metaheuristic #8: simulated annealing random restart.Figure 11.10 Metaheuristic #9: taboo search.Figure 11.11 Metaheuristic #13: evolutionary optimization (darwinian evoluti...
11 Chapter 12Figure 12.1 Left. The general stochastic sequential analysis flow topology. Figure 12.2 CCC protocol flowchart (part 1).Figure 12.3 CCC protocol flowchart (part 2).Figure 12.4 CCC protocol flowchart (part 3).Figure 12.5 PRI Mixture Clustering Test with 4D plot [35 ]. The vertical axi...Figure 12.6 In the figure we show state‐decoding results on synthetic data t...
12 Chapter 13Figure 13.1 Single neuron. Sigma activation function: the inputs x kare mult...Figure 13.2 A five layer neural net.
13 Chapter 14Figure 14.1 A schematic for the U‐tube, aperture, bilayer, and single channe...Figure 14.2 (a) The top panel shows the power spectral density for signals o...Figure 14.3 (a) Standard free energy of hairpin formation vs. shoulder block...Figure 14.4 (a) Event diagram for DNA hairpins with three to eight base‐pair...Figure 14.5 Detection of single nucleotide differences between DNA hairpins....Figure 14.6 Blockade Mechanism. The intermediate level (IL) conductance stat...Figure 14.7 (a) Typical power spectra for captured nine‐base‐pair DNA hairpi...Figure 14.8 Accuracy for classification of single‐species solutions of 9TA, ...Figure 14.9 Classification on a 3 : 1 mixture of 9TA and 9GC hairpin molecul...Figure 14.10 Translocation information and transduction information. (a) Ope...Figure 14.11 Nanopore detector detection topologies involving polymer transl...Figure 14.12 Schematic diagram of the nanopore transduction detector [1, 3]....Figure 14.13 (a) Nanopore transduction detector (NTD) probe – a bifunctional...Figure 14.14 The various modes of channel blockade are shown: I. No channel ...Figure 14.15 Probes shown: bound/unbound type and uncleaved/cleaved type.Figure 14.16 (a) Nanopore epitope assay (of a protein, or a heterogenous mix...Figure 14.17 (a) Oriented modulator capture on protein (or other) with speci...Figure 14.18 Multichannel scenario, with only one blockade present (at low c...Figure 14.19 (a) Channel current blockade signal where the blockade is produ...Figure 14.20 (a) Study molecule with externally driven modulator linkage to ...Figure 14.21 (a) Same situation as in cases with linked‐modulator, but more ...Figure 14.22 External modulations with transducer with coupler, a trifunctio...Figure 14.23 (a) Observations of individual blockade events are shown in ter...Figure 14.24 Pseudo‐aptamer: DNA overhang binding complement – signal blocka...Figure 14.25 Y‐aptamer with DNA overhang that binds complement. (a) Si...Figure 14.26 Eight‐base annealing using a NTD Y‐transducer. (a) ...Figure 14.27 Shown are Y‐shaped aptamers that have shown they have capture s...Figure 14.28 The Y‐SNP with test complex is shown at the base‐level specific...Figure 14.29 The Y‐SNP test complex with 35 dT length overhang is shown at t...Figure 14.30 The thrombin aptamer from [277] is 5′‐CACTGGTAGGTTGGTGTGGTTGGG...Figure 14.31 The determination of aptamers can be done (or initiated) via Sy...Figure 14.32 The standard antibody schematic. Standard notation is shown for...Figure 14.33 Typical antibody N‐glycosylation. A schematic for typical...Figure 14.34 (a) DNA hairpin bound to antibody via an EDC‐linker. Appr...Figure 14.35 DNA‐hairpin signals. (a) No biotin concentration. (b) Low...Figure 14.36 Example that provides a very clear, stable, blockade direct by ...Figure 14.37 Antibody–Antigen binding – clear example from specific capture ...Figure 14.38 Antibody signal classes and Ab‐antigen signal classes. A–...Figure 14.39 Multivalent antigen binding. (a) First antibody–antigen binding...
Читать дальшеИнтервал:
Закладка:
Похожие книги на «Informatics and Machine Learning»
Представляем Вашему вниманию похожие книги на «Informatics and Machine Learning» списком для выбора. Мы отобрали схожую по названию и смыслу литературу в надежде предоставить читателям больше вариантов отыскать новые, интересные, ещё непрочитанные произведения.
Обсуждение, отзывы о книге «Informatics and Machine Learning» и просто собственные мнения читателей. Оставьте ваши комментарии, напишите, что Вы думаете о произведении, его смысле или главных героях. Укажите что конкретно понравилось, а что нет, и почему Вы так считаете.