With the exponential increase of digital connectivity, cyber-physical interfaces (in the Internet of Things), and machine learning and artificial intelligence, it is more important than ever to treat cybersecurity as a science and a business enabler, as opposed to simply a cost of doing business.
We must reveal the connection between fundamental scientific principles and cybersecurity best practices. What are the foundational primitives and rules that would have been beneficial to have at the beginning of the Internet? How would things have been different if they had been in place? How can we create a better form of cybersecurity based on the nature of fundamental forces and accurate assumptions?
Embracing cybersecurity as a science can be an incredibly powerful and effective way to underpin innovation. It will enable us to focus on effectively leveraging the Internet's forces of speed and connectivity as well as one more unchangeable force that we'll talk about later in this book: the fallibility and needs of humans.
It is a bold goal to attempt to make cybersecurity more scientific, but in our view, it is achievable with the right vision and engineering. By doing so, we can further extend the power of speed and connectivity to thrive within the digital world. Rather than suffering through the cosmic big bang's equivalent of the melting of our planet by the death of our sun billions of years from now, let's understand, define, and work within the laws of the science of cybersecurity.
As mentioned earlier, the most fundamental forces of cybersecurity are speed and connectivity. Our solutions must be built to support and leverage these forces.
Although security has historically slowed things down, security without speed is a losing proposition. Similarly, security is only as strong as the weakest link in the chain, so security must enable connectivity—specifically, an integration of your defenses to leverage your strengths. This is a far better core strategy than the common alternative: expecting your weakest point to be better than the adversary's strongest methods. To achieve not only optimal but even basically functional cybersecurity, we must have speed, connectivity, and integrated cybersecurity.
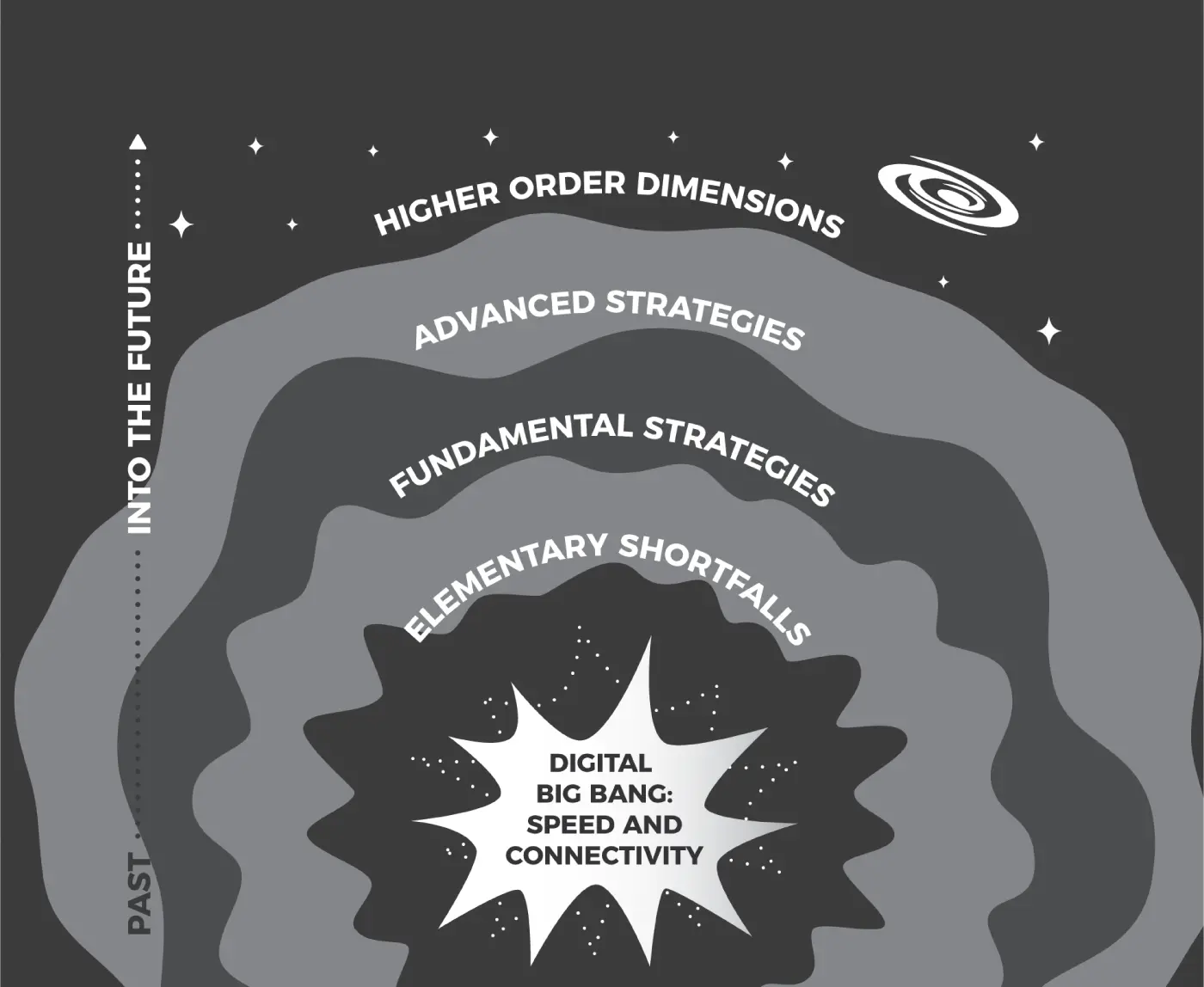
In the pages that follow, we will explore the scientific forces of speed and connectivity that must shape our approach (see Figure 1). We must show how to harness and amplify these forces with cybersecurity that offers greater degrees of precision to counter the increasing sophistication of threat actors and cybercriminals.
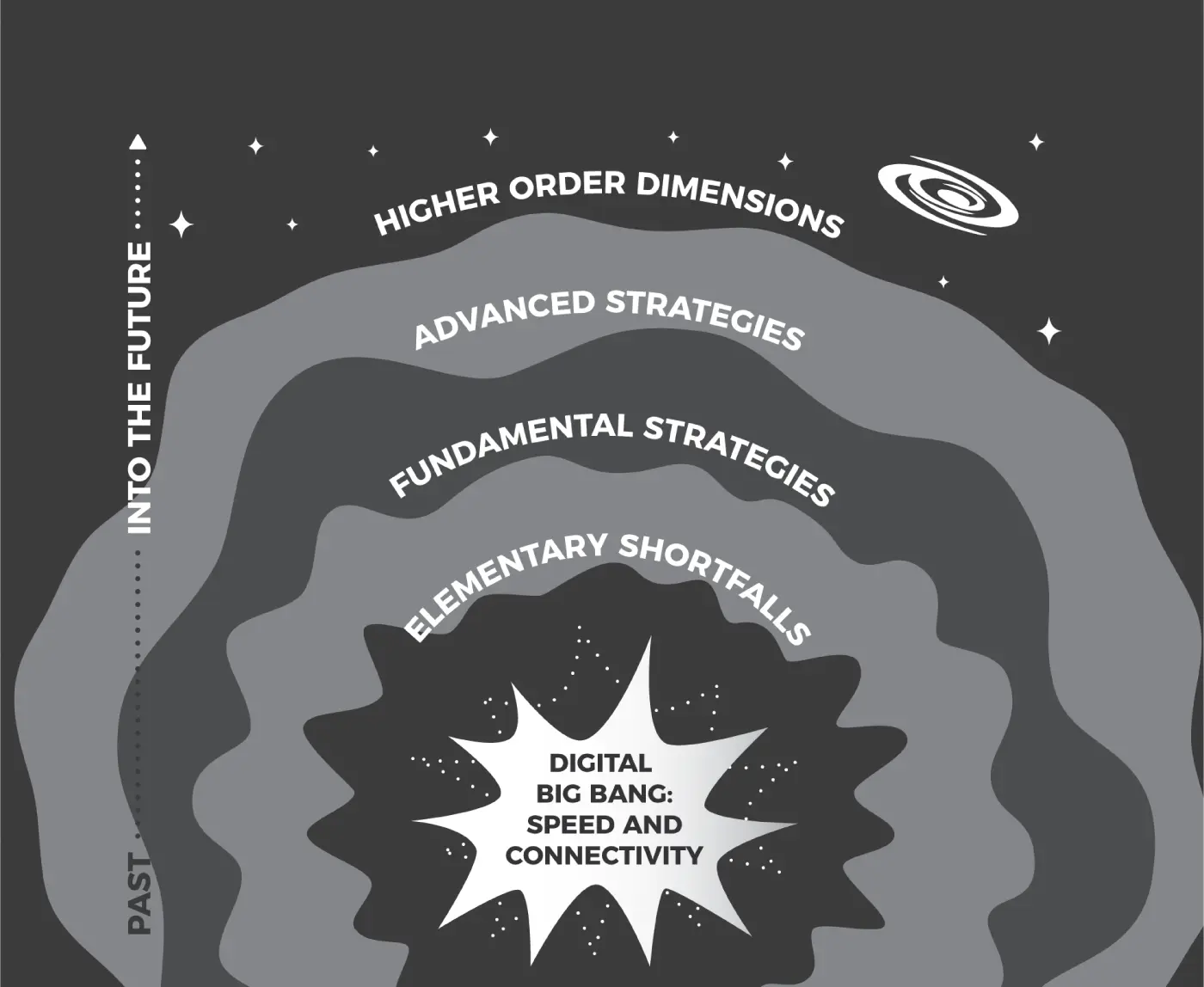
Figure 1 Speed and connectivity form the nucleus of the digital big bang.
We will explore how we can create a more scientific approach to cybersecurity, based on accurate assumptions. We will probe the essence of the modern problems we face and see how lessons from the world of science extend to cyberspace, leading us to certain inevitable mind-expanding conclusions about the very nature and order of how cybersecurity must evolve.
This book is divided into parts. Part Iexplores the digital nucleus of speed and connectivity.
Part IIdetails the elementary shortfalls in the areas of authentication, patching, and training, and Part IIIdiscusses fundamental strategies of access control, cryptography, and segmentation.
Part IVcovers advanced strategies, including visibility, inspection, and failure recovery, and Part Vlays out higher-order dimensions we must account for, including complexity management, privacy, and human frailty.
In keeping with the spirit of the Internet's invention, this book is a collaborative effort. For each of the topics mentioned, we will hear from some of the leading experts in cybersecurity today, across industries and disciplines, as they come together to offer their insights.
We define success as enabling a pace of innovation in the field of security that outruns the inevitable attempts by adversaries to do their dirty deeds.
It is our hope that by focusing on the fundamental and foundational principles of the science of cybersecurity, this book will empower those who fight the battles to achieve more effective, efficient, and consistent victories for many years to come.
SECTION 1 BINDING STRATEGIES:THE CORE OF CYBERSECURITY
The central parallel between the cosmic big bang and the digital big bang rests in their origins. The cosmic big bang unleashed the two central forces of matter and energy, inexorably connecting them in a way that has shaped and driven our entire existence. The invention of the Internet harnessed technological innovation to weld speed and connectivity—the central forces of the digital big bang equivalent to matter and energy—as a means of communication so powerful it has the potential to change the future of the human race.
Because speed and connectivity are the two primary elements of the Internet, harnessing their strengths and managing their risks must be the primary elements of any effective security strategy.
But too often cybersecurity is at odds with speed and connectivity.
The Internet created a game-changing means to increase the velocity of information and the speed at which business can be done—to send data faster, accelerating the rate at which we can connect and communicate with others. Remember the days of sending data on disks through the mail? From those early academic uses, that connection has grown. Now the connection includes large-scale business and personal interests, contains our most sensitive health and financial information, and falls within the private and public sectors. Or we may use that connection for sheer entertainment.
The velocity with which we can now send and receive even massive amounts of data is staggering and getting faster every day. We can search for obscure facts, with answers in seconds; communicate in real time with people all over the world; and buy products with one easy click. Regardless of their use and application, today's systems of digital data transmission were designed to be faster than any other means at the time, and they have consistently exceeded that goal.
But to date, that speed has been a problem for defenders. Defensive systems often leach CPU cycles, forcing communication to slow down. When that happens, users often will simply turn off security features, leaving the network and its data vulnerable to attackers. To succeed, our security strategies must be based on leveraging that core philosophy of doing things at Internet speed.
The Internet's creation was a testament to the power of collaboration. Researchers realized that they could achieve more insightful results by comparing and combining their efforts and getting access to remote computing resources.
The resulting architecture was designed around rich and resilient connectivity. As it matured, the Internet fulfilled deep needs for speed and connectivity—organizational, financial, physical, mental, and even emotional—which catalyzed its unprecedented proliferation.
But that highly desired connectivity also opened the door to attacks. Attackers soon learned that they could use connectivity to their advantage to achieve a malicious effect without being near their actual target. Adversaries now can launch attacks from multiple places, focusing their multifaceted barrage on points of weakness. Perhaps it is the central dilemma of cybersecurity: if you can connect with everybody, you can be reached by anybody.
Читать дальше