1 ...7 8 9 11 12 13 ...18 Cybersecurity operations teams have been developing at an ever‐increasing pace in the last 10 years, especially after the Sony Pictures hack in 2014, which showed that a foe like a state actor with determination and nearly unlimited resources (unlike a script kiddie or even criminal hackers) can get into any company and disclose such deeply embarrassing details. There are firewall and router certifications for ethical hacking and for security that focus solely on finding or preventing the bad actors. However, none of them spend any amount of time on learning how to secure company data at the third parties. Indeed, this is an area for improvement as the cybersecurity professionals begin to learn how to perform at a higher level on third‐party risk.
Business or Technology Risk and Cybersecurity Risk
Many companies of larger size have departments or groups that are designed to manage and report risk for the whole company. These teams are very important as centralized groups for risk management at big organizations. Often, these teams perform the process and compliance work for third‐party risk, including the cybersecurity domain.
While these professionals are trained and certified in how to evaluate risk within an organization, the issue of evaluating cybersecurity risk produces better results when performed by trained and certified cybersecurity professionals. The cybersecurity domain is very complex, as illustrated in the section titled “Cybersecurity and Third‐Party Risk.” Even within the field, there are numerous specialty fields and certifications along with a fast‐changing environment. Expecting a generalist risk professional to opine on controls for information security topics might produce adequate, but not necessarily accurate, data.
In cases where a risk organization consists of general risk professionals who don't have the specialty training and experience of cybersecurity professionals, it is optimal if these professionals, like the TPRM team, collaborate with the cybersecurity teams at their company for that level of expertise.
Cybersecurity Third‐Party Risk as a Force Multiplier
Military science uses a term called force multiplier , which refers to a combination of circumstances that gives personnel the ability to amplify their normal capabilities to achieve greater goals. In modern times, the Global Positioning System (GPS) has been a force multiplier, as it enabled more personnel to be moved at a faster pace due to the capabilities added from the technology. In the U.S. Special Forces, a lot of time is spent on creating and training local fighter forces as a form of a force multiplier. The small force of a 12‐man unit can go out and lead a unit of 100–200 local fighters. The force multiplier here is the U.S. Special Forces troops growing in strength from 12 to 200. A cybersecurity team, partnering with TPRM, can be a force multiplier to strengthen the risk management of third parties.
As understood, the cybersecurity field is complex and full of certifications, specialties, technical details, and domains. This complexity can be simplified for a TPRM team when a specialized team of cybersecurity professionals are able to execute on an active threat hunting mentality in reference to third parties. The whole TPRM and business risk teams do not have to be experts in information security, but they can use the force multiplier effect of a few good cybersecurity special forces. These special forces are trained to monitor security controls at vendors, to ensure that enemy forces are reined in by contractual obligations, to constantly watch for new threats, and to partner with vendors to train their local forces to better fight the enemy directly. The collaboration and teamwork between the cyber and TPRM professionals continually sharing and updating reference documents multiplies the strengths of both teams.
TPRM must grow its strength in cybersecurity. Cybersecurity must increase its own research, resources, and results on third‐party risk. For those in business and cybersecurity as well as TPRM, this is an opportunity to exponentially grow cybersecurity across industries. If the TPRM process grew its cybersecurity with a force multiplier approach, and cybersecurity research and resources were focused more on third‐party risk, we would more broadly adopt what is required: a rethink of cybersecurity and third‐party risk. This adoption would include a practice around vendor risk management that places cybersecurity at the forefront, and a cybersecurity team that uses the same resources as cyber operations threat analysts.
The earlier statistic that stated the average company is connected with 600 vendors with PII becomes the exponential part. As more companies adopt a cybersecurity and third‐party risk approach and are able to partner with these vendors, across multiple industries, we get real security change across all the third parties. It's a simple math equation: It becomes a multiplier for better corporate information security across the globe.
The evidence of the risk exists: At the end of 2020, in one month there were three nation‐state APT attacks that exploited weaknesses in supply chain cybersecurity. Two of them were aimed at two countries: Mongolia and Vietnam. The damage and scope of the SolarWinds Orion exploit is not yet known as more victims are being uncovered, but it does include big names in technology and major government systems globally. The advanced persistent actors (i.e., hackers) are clearly targeting and weaponizing the supply chain. They have discovered that third‐party cybersecurity is the weakest link to their actual targets.
The investment that CISOs and cybersecurity professionals have made in the last 20 years has been proven effective in many ways. Most companies and governments that know they will be a target (due to size, money, power) have beefed up their own cybersecurity. But behind these medium and large organizations are thousands or millions of smaller companies that are focused on selling, not securing, their data. Cybersecurity can lean into this area more forcefully, trying and implementing new capabilities learned from other cyber domains and leadership. The need is to take Cybersecurity Third‐Party Risk from a compliance‐driven effort to an active always learning, always searching for risk approach in order to lower risk from vendors.
Chapter 2 Cybersecurity Basics
While this book does not require the reader to be either a risk expert or cybersecurity expert, given there will be terminology and process discussions on some cybersecurity topics, some time spent on the terminology and the subject matter is warranted.
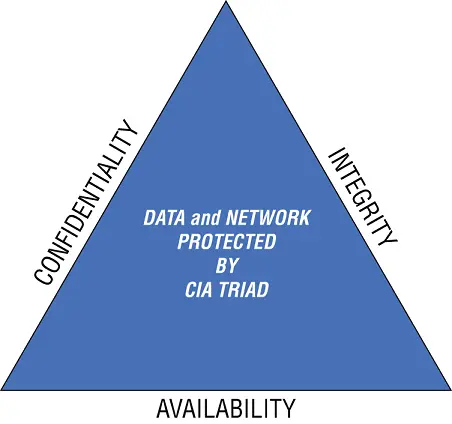
Cybersecurity has three main pillars: Confidentiality, Integrity and Availability (CIA):
Confidentiality: Prescribes only authorized users and systems should be able to access or modify data.
Integrity: Data should be maintained in a correct state and cannot be improperly modified.
Availability: Authorized users should be able to access data when needed.
This is called the CIA Triad as shown in Figure 2.1.
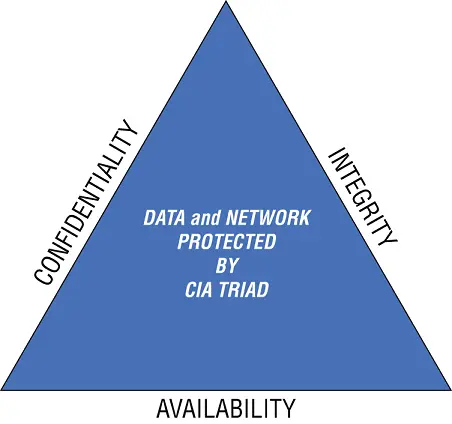
FIGURE 2.1The CIA Triad
These pillars are designed to break down the complexities of cybersecurity to determine how to best make decisions. For example:
Does the vendor store our data in ways that make it more secure?
Will this product ensure the integrity of our data in the cloud?
Can the vendor ensure that the data will be available when required to those who need it?
Because this book is mainly focused on third parties, references will be aligned with that focus in mind. It is not about what security your organization is performing, but what is going on at the third party, both with the specific services they provide and also how they secure their own enterprise. We include several examples of how a vendor's connection is used to target a company, and how their company‐wide cyber controls directly impact the ability to protect a company's data and any connection to your network (both intermittent and persistent).
Читать дальше
![Stephan Orth - Behind Putin's Curtain - Friendships and Misadventures Inside Russia [aka Couchsurfing in Russia]](/books/415210/stephan-orth-behind-putin-s-curtain-friendships-a-thumb.webp)