Cynthia Brumfield - Cybersecurity Risk Management
Здесь есть возможность читать онлайн «Cynthia Brumfield - Cybersecurity Risk Management» — ознакомительный отрывок электронной книги совершенно бесплатно, а после прочтения отрывка купить полную версию. В некоторых случаях можно слушать аудио, скачать через торрент в формате fb2 и присутствует краткое содержание. Жанр: unrecognised, на английском языке. Описание произведения, (предисловие) а так же отзывы посетителей доступны на портале библиотеки ЛибКат.
- Название:Cybersecurity Risk Management
- Автор:
- Жанр:
- Год:неизвестен
- ISBN:нет данных
- Рейтинг книги:3 / 5. Голосов: 1
-
Избранное:Добавить в избранное
- Отзывы:
-
Ваша оценка:
- 60
- 1
- 2
- 3
- 4
- 5
Cybersecurity Risk Management: краткое содержание, описание и аннотация
Предлагаем к чтению аннотацию, описание, краткое содержание или предисловие (зависит от того, что написал сам автор книги «Cybersecurity Risk Management»). Если вы не нашли необходимую информацию о книге — напишите в комментариях, мы постараемся отыскать её.
Cybersecurity Risk Management: Mastering the Fundamentals Using the NIST Cybersecurity Framework
Cybersecurity Risk Management
Cybersecurity Risk Management
Cybersecurity Risk Management — читать онлайн ознакомительный отрывок
Ниже представлен текст книги, разбитый по страницам. Система сохранения места последней прочитанной страницы, позволяет с удобством читать онлайн бесплатно книгу «Cybersecurity Risk Management», без необходимости каждый раз заново искать на чём Вы остановились. Поставьте закладку, и сможете в любой момент перейти на страницу, на которой закончили чтение.
Интервал:
Закладка:
Brian Haugli
May 2021
Preface – Overview of the NIST Framework
The National Institute of Standards and Technology (NIST), located in Gaithersburg, MD, is a US Department of Commerce division. It is assigned the job of promoting innovation and industrial competitiveness. It is a research organization filled with some of the world’s leading scientists and has produced many Nobel Prize winners.
NIST has a wide-ranging mandate: develop federal patents, oversee over 1,300 Standard Reference Materials, run a scientific laboratory in Boulder, CO, and pursue innovation in encryption technologies, among other significant efforts. NIST is primarily a scientific and engineering organization and, as such, produces patents, technical breakthroughs, documentation, and recommendations through extensive consultation with experts in various areas. This scientific consensus approach often has impressive results that can be difficult for non-specialists to understand or apply.
The NIST Cybersecurity Framework resulted from an intensive one-year effort to synthesize cybersecurity experts’ best thinking into a single “framework of frameworks” that can assure superior risk management. It’s well-understood in the cybersecurity field that risks are constant and that the best approach to organizational cybersecurity is to manage those risks because no one can eliminate them.
The NIST Framework attempts to incorporate all the best various risk management and remediation practices into one coherent whole, an ambitious goal in the complex cybersecurity field. It is a multi-layered, spoke-and-wheel collection of ideas grouped along logical lines.
The Framework is conceptual and not technical, making it a challenge for many organizations to apply in the real world. It doesn’t help that NIST specifically avoided any technical recommendations when developing the Framework. NIST instead chose to map its recommendations to a host of standards, or informative references, designed in-house and at other standards-setting bodies.
Despite its growing use among leading corporations, government offices, and non-profit organizations in the United States and worldwide, many non-cybersecurity professionals, and even some cybersecurity specialists, struggle with the practical application of the NIST Framework.
The following summary provides a broad overview of what the Framework is and how it’s structured. Keep in mind that the rest of the book focuses on the much-needed practical guidance on applying the NIST Framework, which we hope even non-cybersecurity professionals will grasp and find useful.
BACKGROUND ON THE FRAMEWORK
In the face of growing concerns over the prospect of a devastating cyberattack on US critical infrastructure, President Barack Obama issued on February 12, 2013, Executive Order (EO) 13636 “Improving Critical Infrastructure Cybersecurity.” 1The EO aimed to create a “partnership with the owners and operators of critical infrastructure to improve cybersecurity information sharing and collaboratively develop and implement risk-based standards.” To achieve that objective, the EO mandated that NIST develop within one year “a voluntary risk-based Cybersecurity Framework, a set of industry standards and best practices to help organizations manage cybersecurity risks.”
To hammer out the Framework, NIST hosted five workshops at multiple universities involving thousands of domestic and international private- and government-sector participants. Finally, on February 12, 2014, NIST issued the Framework for Improving Critical Infrastructure Cybersecurity . 2The Department of Homeland Security (DHS) currently considers 16 sectors to be critical infrastructure sectors, encompassing information technology, financial services, energy, communications, manufacturing, and many other central services. 3However, NIST hopes that the Framework will be helpful to all organizations and anticipates that its application will extend beyond critical infrastructure.
Underscoring the “living” nature of the Framework, on April 16, 2018, NIST issued an update, Version 1.1. 4The updated Framework features several additional subcategories, including an expansive new set of subcategories dealing with Supply Chain Risk, a timely addition as the protection of digital supply chains has taken center stage due to some recent damaging and high-profile supply chain attacks.
In developing the Framework, NIST wanted to ensure maximum flexibility of application. The final document is industry- and technology-neutral. It encompasses hundreds of standards. It is also international in scope.
NIST stresses that the Framework is not intended to replace any organization’s existing cybersecurity program but is a tool to strengthen existing practices. Suppose an organization does not have a cybersecurity risk management program or set of cybersecurity practices in place? In that case, the Framework should serve as a good starting point for developing that program or those practices.
FRAMEWORK BASED ON RISK MANAGEMENT
NIST premised the entire Framework on the concept of risk management, which is “the ongoing process of identifying, assessing, and responding to risk,” an approach that provides a dynamic implementation of the Framework’s recommendations. Under a risk management approach, “organizations may choose to handle risk in different ways, including mitigating the risk, transferring the risk, avoiding the risk, or accepting the risk, depending on the potential impact to the delivery of critical services.” 5
The Framework consists of three parts: The Framework Core, the Framework Implementation, and the Framework Profile Tiers. The purpose of these three parts is to provide a “common language” that all organizations can use to understand, manage, and communicate their cybersecurity initiatives, both internally and externally, and can scale down or up to various parts of an organization as needed.
THE FRAMEWORK CORE
The Framework Core is a set of activities aimed at organizing cybersecurity initiatives to achieve specific outcomes. The Core has five functions: Identify, Protect, Detect, Respond, and Recover (Figure 0.1).
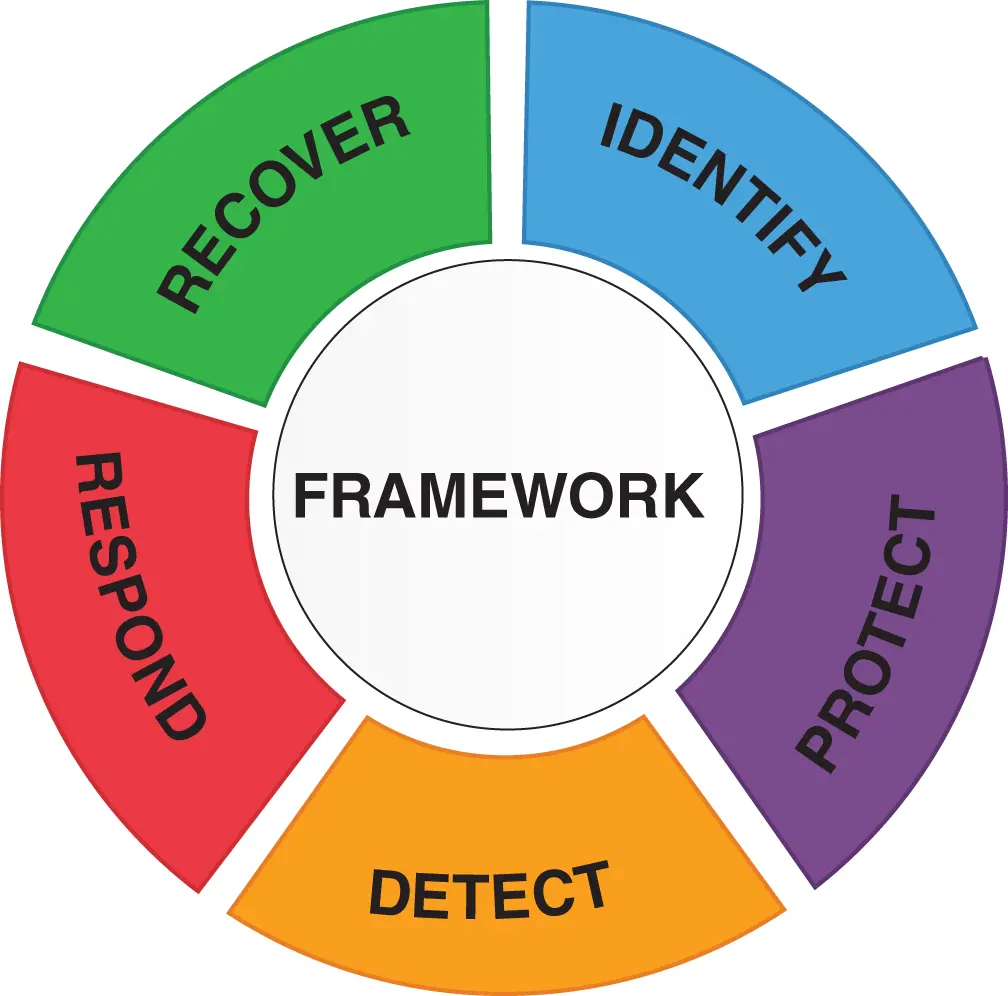
Figure 0.1 NIST CORE FRAMEWORK.
Within each of these functions are categories of activities. Within each category of activities are subcategories, and for each subcategory, there are informative references, usually standards, for helping to support the activities (Figure 0.2).
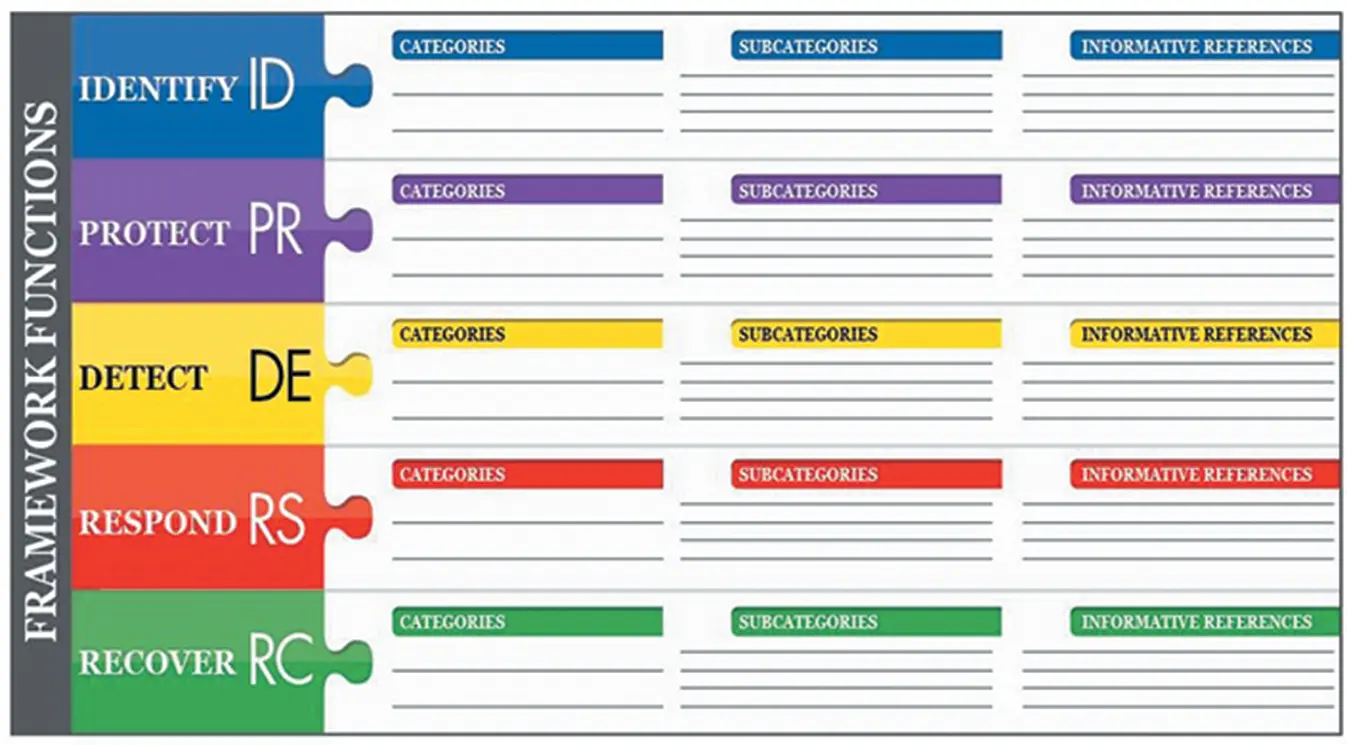
Figure 0.2 NIST CATEGORIES, SUBCATEGORIES, AND INFORMATIVE REFERENCES.
For example, one category under the function Identify is Asset Management (Figure 0.3). A subcategory of Asset Management is “Physical devices and systems within the organization are inventoried.” For that subcategory, the Framework offers informative references that guide physical devices’ inventory, mostly standards established by various technical standards-setting bodies. The complete listing of the Functions, Categories, Subcategories, and Informative References are in Appendix A of the final Framework Document on the NIST website. 6
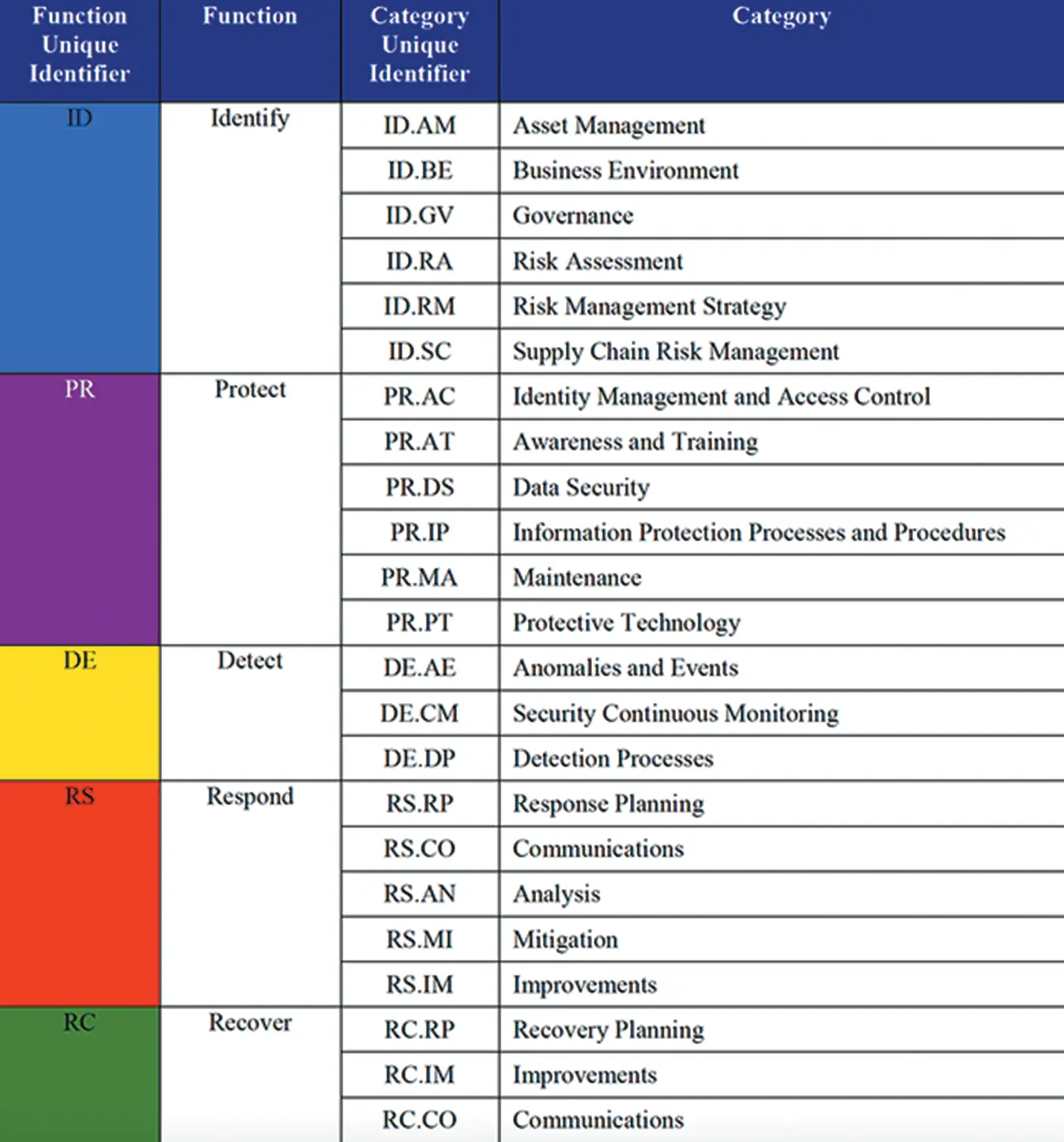
Figure 0.3 NIST FUNCTIONS AND CATEGORIES.
Читать дальшеИнтервал:
Закладка:
Похожие книги на «Cybersecurity Risk Management»
Представляем Вашему вниманию похожие книги на «Cybersecurity Risk Management» списком для выбора. Мы отобрали схожую по названию и смыслу литературу в надежде предоставить читателям больше вариантов отыскать новые, интересные, ещё непрочитанные произведения.
Обсуждение, отзывы о книге «Cybersecurity Risk Management» и просто собственные мнения читателей. Оставьте ваши комментарии, напишите, что Вы думаете о произведении, его смысле или главных героях. Укажите что конкретно понравилось, а что нет, и почему Вы так считаете.