Cyber Security and Network Security
Здесь есть возможность читать онлайн «Cyber Security and Network Security» — ознакомительный отрывок электронной книги совершенно бесплатно, а после прочтения отрывка купить полную версию. В некоторых случаях можно слушать аудио, скачать через торрент в формате fb2 и присутствует краткое содержание. Жанр: unrecognised, на английском языке. Описание произведения, (предисловие) а так же отзывы посетителей доступны на портале библиотеки ЛибКат.
- Название:Cyber Security and Network Security
- Автор:
- Жанр:
- Год:неизвестен
- ISBN:нет данных
- Рейтинг книги:3 / 5. Голосов: 1
-
Избранное:Добавить в избранное
- Отзывы:
-
Ваша оценка:
- 60
- 1
- 2
- 3
- 4
- 5
Cyber Security and Network Security: краткое содержание, описание и аннотация
Предлагаем к чтению аннотацию, описание, краткое содержание или предисловие (зависит от того, что написал сам автор книги «Cyber Security and Network Security»). Если вы не нашли необходимую информацию о книге — напишите в комментариях, мы постараемся отыскать её.
Written and edited by a team of experts in the field, this is the most comprehensive and up-to-date study of the practical applications of cyber security and network security for engineers, scientists, students, and other professionals.
Cyber Security and Network Security — читать онлайн ознакомительный отрывок
Ниже представлен текст книги, разбитый по страницам. Система сохранения места последней прочитанной страницы, позволяет с удобством читать онлайн бесплатно книгу «Cyber Security and Network Security», без необходимости каждый раз заново искать на чём Вы остановились. Поставьте закладку, и сможете в любой момент перейти на страницу, на которой закончили чтение.
Интервал:
Закладка:
Due to the rapidly growing virtual market, data is at its abundance as starting from the startup companies, companies from the MSME sector and even the traditional core large companies are shifting and changing their business model to adapt to cloud. Thus, security of the applications along with the data has become a necessity rather than a choice.
Due to the rapidly increasing demands, which are producing a large amount of data, the users are facing problems of securely storing that data in a searchable format. Studies have also suggested that security and privacy are among the major factors of influencing a consumer’s trust [1, 2]. Some researchers have worked upon the concept of securing the data through blockchain. However, blockchain integration makes the computations required, and unnecessarily complex and large computations of the blockchain are quite unnecessary when thinking of saving data that are important but come in too frequently. This concept was not introduced to just storing data cryptographically but from the concept of “transfer of assets from peer to peer”.
Thus, in our proposed model, our objective is to help the data from users, (here) an enterprise software transfer their data through the public network by the use of a web-based software, facilitating encrypted communications over the public channels and keeping unnecessary computations to its bare minimum. Data, be it object-based or text or JSON data structure, can be passed through the system and can be checked up for malware. If the data transmitted is seen to be coming in through valid credentials and passes the security checks, then it would be stored in the NoSQL databases. For object-based files, the files would be checked for security exploits, and after passing the checks, it would be checked if the files could be scaled down and they would be saved over in the object storage buckets. Logs would be generated for every action undertaken by the user after log in and those corresponding logs would be added on to immutable ledger databases for further audits and checks with timestamps, so that every user in the system is accountable for their actions.
The proposed system has a highly scalable and available architecture. The number of systems provisioned in the architecture can grow/shrink according to the load. The proposed system is developed keeping in mind that the data stored can be queried easily, so that it can serve as a better alternative to the proposed blockchain systems that are being proposed widely. The suggested architecture can also check for intrusion and can perform malware analysis, spam detection, etc.
1.2 Background and Related Works
Every device produces metadata based on the client’s request. For securing cloud base applications, metadata exchange is also necessary to maintain nondisrupting service. Any hacker can easily take advantage of those metadata and use that for any malicious intention like malware injection and many others. In this case, a hacker needs to inject malicious code or service of the valid instance running in the cloud. If the hacker is successful, then the cloud will suffer from deadlocks and eavesdropping which forces real users to wait until the process is not completed. This type of attack is also known as metadata spoofing attack. In this way, anyone can get access to the cloud easily [3, 4].
Imagining that Raspberry Pi is connected to the internet using a wireless router and it sends data to the cloud. Here, if any hacker joins the network, then he places himself between two communicating parties and relaying messages for them. Here, the hacker is also getting full access to the data, and he can also monitor and change the contents of messages.
SQL injection is an attack that toxins dynamic SQL statements to comment out certain parts of the statement or append a condition that will ceaselessly be true. It takes advantage of the planning flaws in poorly designed net applications to require advantage of SQL statements to execute malicious SQL code. Thus, in our proposed approach, we have used a NoSQL database. In a NoSQL database, traditional SQL injection should not cause a risk to the system.
If only HTTPS is used and data is not encrypted, then it is in readable form before being sent to a private network, so it can be manipulated by any third person intriguing in the system. So, SSL Certificate (Secure Socket Layers) is used which ensures that it remains impossible for anyone else other than the receiver and sender to read the data by using encryption algorithms already integrated in it. However, HTTPS can be decoded using SSL man in the middle (MITM) through various ways. One of them is enabling the packet routing feature on hacker machines and running a DNS spoof so that the victim connects to hacker machine through HTTP/ HTTPS port [5].
In the paper “Security Enhancement for Data Migration in the Cloud”, J. R. N. Sighom et al. discussed regarding securing data in the cloud are one of the key roles. To maintain the privacy and security of data, researchers have combined several encryption algorithms like IDA (Information Dispersal Algorithm), SHA 512 (Secure Hash Algorithm), and AES 256 (Advanced Encryption Standard). The encrypted data is split into several parts. During the decoding process, the validation stages are observed first. IDA is used after the reconstruction of encrypted data, and it is reconverted into the initial data using AES 256. Consistent with the result, the common execution time is higher when the decoding time process is verification 1.453 [6].
Researchers have also tried to improve the security of data in the cloud by using the DES (Data Encryption Standard) and AES (Advanced Encryption Standard) algorithm together. Cloud computers well describe the set of resources or services that it offers on the internet, to meet the requirements of cloud providers [7].
Cloud computing systems have come a long way in implementing and executing applications in a sandboxed environment minimizing threat, and maximizing reliability, scalability, availability, and security. Although there has been much research to make the cloud platforms interoperable in between multiple organizations by organizing and reorganizing the cloud federation [8, 9], i.e., giving the companies the power to collaborate and share resources among each other. Multiple federation architecture is being proposed such as cloud brokering, aggregation, and cloud bursting and is worked upon to find out the most suitable among them [10]. However, there have been issues of portability and interoperability among them [11]. Primarily, the partially coupled federation is being followed where the company private servers and the services hosted on the public cloud are interoperable and there is an understanding and sharing of resources between the servers depending on the flow of traffic and load.
1.3 System Design and Architecture
1.3.1 Proposed System Design and Architecture
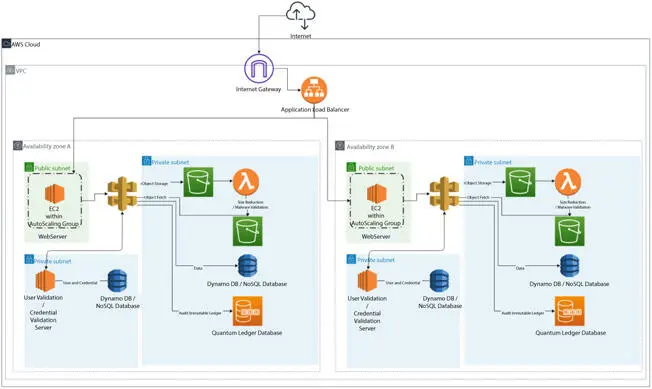
Figure 1.1 Proposed system design architecture.
1.3.2 Modules
1.3.2.1 Compute Instances
Amazon Elastic Compute Cloud, commonly known as EC2, is a computer service provisioning virtual servers on demand. The instances can be autoscalable based on requirements, and it is highly flexible as one instance can be launched in a few minutes and configured to cater the needs. The web server applications are hosted on the servers. The servers are configured to be autoscalable and to scale out on the occasion of high traffic or load. On the occasion that the CPU or memory remains unutilized, then the autoscaling further kicks in to scale-in the number of compute instances to save resources. Figure 1.1shows proposed system design architecture.
Читать дальшеИнтервал:
Закладка:
Похожие книги на «Cyber Security and Network Security»
Представляем Вашему вниманию похожие книги на «Cyber Security and Network Security» списком для выбора. Мы отобрали схожую по названию и смыслу литературу в надежде предоставить читателям больше вариантов отыскать новые, интересные, ещё непрочитанные произведения.
Обсуждение, отзывы о книге «Cyber Security and Network Security» и просто собственные мнения читателей. Оставьте ваши комментарии, напишите, что Вы думаете о произведении, его смысле или главных героях. Укажите что конкретно понравилось, а что нет, и почему Вы так считаете.